Sophos Firewall
The heart of the world’s best network security platform
Consolidate, simplify, and save with a firewall that's Secure by Design. Get unmatched protection, powerful performance, streamlined management, and superior value for your hybrid networked world.

What you get:

Secure by Design
Hardened from the code to the core with automatic patching, a health check for risky configurations, and remote integrity monitoring by Sophos.

Powerful protection and performance
AI zero-day protection and performance that improves with every release thanks to the XGS Series appliances and the next-gen Xstream Architecture.

Unmatched Detection and Response
Stops attacks dead in their tracks with unique capabilities like integrated NDR, Synchronized Security, and Active Threat Response.

Single Management Console
Easily manage your network and all your cybersecurity from a single cloud console, including switches, wireless, workspace, messaging, endpoint, and more.
Secure by Design
In the AI era, Secure by Design isn't optional — it's how you keep your network secure
Sophos Firewall is the most secure and hardened firewall on the market, with unique features like automated patching, configuration health check, and remote integrity monitoring.
Powerful Protection and Performance
Industry-leading price-per-protected-Mbps that gets better with every update.
Powered by Xstream
The Sophos Xstream architecture accelerates and offloads important traffic and crypto operations to the FastPath to maximize performance. The best part is, our architecture is programmable, so it gets new protection and performance enhancements with nearly every release.
Intelligent detection of encrypted threats
Sophos Firewall removes an enormous blind spot in your traffic, with intelligent TLS decryption that won’t slow you down. Plus, with NDR built-in, you get AI detection of encrypted threats without even having to decrypt the traffic.
AI powered zero-day threat protection
Sophos Firewall uses several AI and ML models to analyze traffic and files to identify the latest unseen threats attempting to get onto your network. Deep packet inspection, AI analysis, and dynamic sandboxing ensure you’re getting the best protection possible.
Stop active attacks dead in their tracks
The only firewall with automatic threat detection AND response.
Detect active adversaries with NDR
Sophos Firewall is the only firewall that integrates AI-powered Network Detection and Response (NDR) to detect active attacks that most other solutions miss. NDR is a product you normally only see in large enterprise networks - and we make it available to everyone in Sophos Firewall - at no extra cost.
Active Threat Response
Sophos Firewall supports a variety of Sophos and third-party threat feeds that provide actionable threat intelligence. If a threat is detected from any of these feeds, the firewall will automatically respond by blocking that device and initiating an automated cross-product Synchronized Security response.
Synchronized Security prevents lateral movement
Sophos Firewall is unique in continuously communicating and sharing information with other Sophos products to automatically respond to threats, coordinating with Sophos Endpoint, Sophos Workspace Protection, and Sophos Email to isolate attacks and prevent lateral movement until they are cleaned up.
Consolidate your cybersecurity
Sophos Firewall is much more than a firewall — it's the heart of the world's best network security platform. Consolidate and simplify your cybersecurity with a single vendor, cloud management console, and agent.
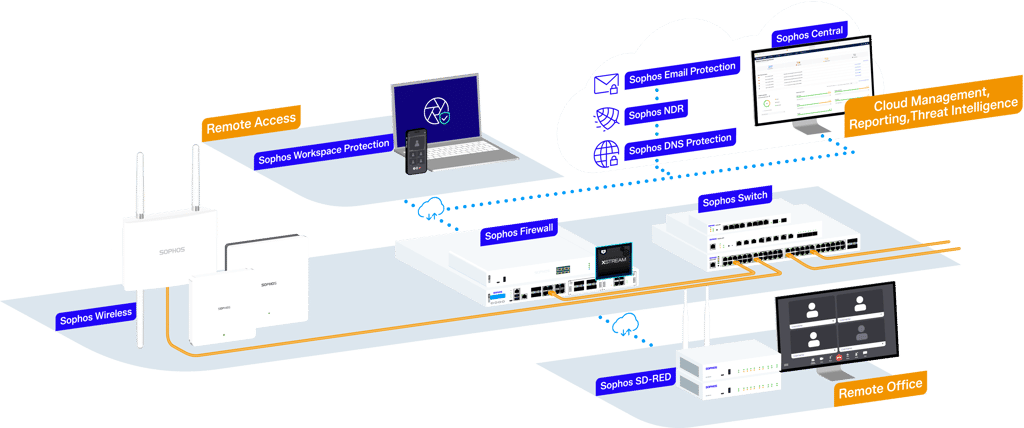
Single Management Console
Sophos Central provides a single pane of glass to manage your firewalls, network infrastructure, workspace, and all your other cybersecurity products.
One console to manage it all
Streamline your cybersecurity management with a single cloud console for your firewalls, switches, wireless, email, endpoints, workspace protection and more.
Rich reporting and orchestration included
Most charge extra for rich reporting and dashboarding – not Sophos. You get unmatched visibility into network activity and point-and-click VPN orchestration tools to make setting up your distributed network easy.
Group firewall management and zero-touch deployment
Sophos Firewall makes it easy to keep a large distributed network in sync, with consistent protection and polices enforced system-wide. It’s also easy to extend your network with simple zero-touch deployment of either firewalls or SD-RED VPN edge devices – and we don’t charge extra for it.
Simplify your move to Sophos Firewall
Enjoy a smooth, seamless transition to Sophos Firewall with our migration tools and resources. We recommend working with a qualified Sophos partner to guide your deployment.
Get the migration guide - 5 essential steps to a successful migration
Explore Sophos Firewall Config Studio - Analyze, edit, and convert your firewall configuration
Speak to your Sophos partner to learn about our attractive migration offers that make it even easier to strengthen your network security.
Sophos Firewall includes more than any other firewall
With the Xstream Protection bundle on Sophos Firewall, you get a several capabilities that other vendors don’t even offer, or charge extra for:

Secure by Design
Sophos Firewall is the most secure firewall on the market with unique features like automated hotfixes, health check for misconfiguration, and proactive monitoring by Sophos for signs of an attack

Leading price-per-protected-Mbps
The best price-per-protected-Mbps in every model of our XGS Series means you're getting the best value. With our programmable Xstream Architecture your performance and protection will actually improve over time – without upgrading your hardware.

AI-powered zero-day detection
Sophos continues to lead in leveraging advanced AI for detections across several vectors, including on-box DPI scanning, cloud-based NDR analysis, static file analysis, and dynamic sandboxing.

ZTNA gateway
An integrated ZTNA gateway enables you to easily deploy ZTNA (included in Sophos Workspace Protection) to your remote and hybrid workers, allowing secure access to internal resources without deploying anything extra.
Comprehensive SD-WAN
Sophos Firewall integrates a complete SD-WAN solution with powerful point-and-click orchestration tools, flexible link management, and performance-based, zero-impact failover.
DNS Protection
Sophos Firewall integrates our global DNS protection service to provide an added layer of web protection across all ports, protocols, and applications.
NDR
NDR is an advanced, AI-powered detection solution that is normally only found in enterprise deployments. Sophos includes an NDR cloud analysis capability to detect threats that would otherwise be missed - something no other firewall offers.

Cross-product automation and Synchronized Security
Sophos is a pioneer in cross-product automation and response to active threats, automatically isolating a compromised host across firewall, endpoint, switch, wireless, email, and workspace protection. No one makes automated response easier than Sophos.
MDR and XDR Integration
Sophos Firewall is unique in being a fully "MDR-ready" firewall, not only by providing unmatched telemetry, but also enabling Active Threat Response for analysts to shut down identified threats immediately without having to setup firewall rules.

Cloud management and reporting
You get streamlined, secure cloud management to manage all your Sophos Firewalls and other Sophos products with features like zero-touch deployment included - it’s like a force multiplier for your team.
Solutions that fit your needs
Sophos Firewall adapts to your network, so you don’t need to adapt your network to your firewall.
Don’t take our word for it
Sophos Firewall is highly rated by organizations across review sites, including Gartner Peer Insights and G2.

Recognized as the #1 Overall firewall solution by G2 users
Frost & Sullivan Competitive Strategy Leadership Award

Gartner® Peer Insights™ Customers' Choice for Network Firewalls 2024
What are you waiting for?
Frequently asked questions
A traditional firewall controls traffic based on IP addresses, ports, and protocols. A next-generation firewall (NGFW) goes further by recognizing applications and users, inspecting encrypted traffic, and blocking advanced threats with integrated intrusion prevention and deep packet inspection. NGFWs provide stronger protection for modern, cloud-connected environments.
A firewall is essential, but it is not enough on its own. Modern environments include cloud services, remote users, encrypted traffic, and connected devices that expand the attack surface. Firewalls work best as part of a layered security strategy that includes endpoint protection, identity controls, monitoring, and threat response.
Yes. Cloud providers secure their infrastructure, but you are responsible for protecting your workloads, users, and configurations. A cloud-capable firewall helps enforce consistent security policies, control traffic between environments, and extend protection across on-prem, cloud, and hybrid networks — all from centralized management.
Modern firewalls provide visibility into users, applications, and encrypted traffic. They log activity, enforce granular policies, and integrate with centralized management platforms. This gives IT teams clearer insight into network activity and helps them respond faster to potential threats.
Firewalls secure connections between remote users, branch offices, and cloud applications. They can enforce policies consistently across locations, support VPN or Zero Trust Network Access (ZTNA), and inspect traffic to prevent threats from spreading across distributed environments.
Focus on three areas: security effectiveness, performance with protections enabled, and ease of management. Look for strong threat prevention, encrypted traffic inspection, centralized policy management, and the ability to scale across on-prem, cloud, and hybrid environments.
In Zero Trust and Secure Access Service Edge (SASE) models, firewalls act as secure control points that enforce least-privilege access and segmentation. They work alongside cloud-delivered security services to extend protection closer to users and applications while maintaining consistent policy enforcement.
- Secure by Design is a software development philosophy that treats security as a foundational requirement rather than an afterthought. Instead of building a product first and bolting on security fixes later, Secure by Design demands that security considerations are embedded into every stage of the development lifecycle — from architecture and design through coding, testing, deployment, and maintenance.
In an AI‑accelerated era, Secure by Design is no longer optional - it’s essential. This shift changes both how vulnerabilities are discovered and how organizations must respond in three fundamental ways:
- Speed: Vulnerabilities are discovered at machine speed, so firewalls must reduce exposure by eliminating entire classes of vulnerabilities.
- Scale: The volume of vulnerabilities discovered is unprecedented, so firewalls must automate patching to reduce the window of exposure.
- Scope: AI lowers the barrier to entry for attackers, so firewalls must be actively monitored as a security asset—not treated as a black box.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)










