Threat Prevention
Stop threats with detection and response across endpoints, network, and cloud workloads.
Advanced threats are outpacing existing security technologies. Organizations need intelligent and automated defense for their networks, endpoints, and cloud workloads to defeat the sophisticated new adversaries. Sophos’ advanced threat prevention technologies offer your organization a multi-layered approach for the widest range of protection from latest threats.
Safeguard your endpoints
Sophos Intercept X, the world's best endpoint protection and cybersecurity services combine deep learning AI, anti-ransomware capabilities, exploit prevention, active adversary mitigations, and other techniques.
Deep Learning Technology
Detect both known and never-before-seen malware without relying on signatures with Deep Learning neural networks built into Sophos Intercept X.
Advanced Anti-Ransomware
Stop ransomware and boot record attacks with Intercept X’s advanced anti-ransomware capabilities like ransomware file protection, automatic file recovery, and behavioral analysis.
Endpoint Detection and Response
Go beyond the endpoint and incorporate cross-product data sources for even more visibility and the ability to drill down into granular detail.
Managed Detection and Response
Proactively hunt threats 24x7 and neutralize even the most sophisticated threats with our managed detection and response services backed by an elite team of threat hunters and response experts who take targeted actions on your behalf.
Protection for All Endpoints
Get complete protection for all your endpoints – desktops, laptops, servers, tablets, and mobile devices across all major operating systems.
Security at the network perimeter
Sophos Firewall integrates a full suite of modern threat protection technologies that enable you to contain threats, automatically block malware from spreading or exfiltrating data out of the network. Get unmatched visibility, protection, and performance for the most demanding networks of today.
Automatic detection and response
High-fidelity detection
We combine deterministic and machine learning models to spot suspicious behaviors and the tactics, techniques, and procedures used by the most advanced adversaries.
Proactive defense
Sophos Intercept X with XDR proactively protects your environment by combining threat intelligence with newly-discovered indicators of compromise identified through threat hunts.
Extended detection and response
Sophos XDR goes beyond the endpoint sending rich network, email, cloud, and mobile data sources to the Sophos Data Lake, a cloud repository for critical XDR and offline device data. Cross reference indicators of comprise from multiple data sources help you quickly identify, pinpoint, and neutralize a threat.
Elite expertise
Our highly-trained team of threat hunters, engineers, and ethical hackers has your back 24/7 with Sophos Managed Detection and Response and Emergency Incident Response, investigating anomalous behavior and taking action against threats.
Cloud workload protection
Secure your AWS, Azure, and GCP cloud environments from the latest threats.
Detect Insecure Deployments
Detect insecure deployments, suspicious access events, over-privileged IAM roles, unusual network traffic, and also reduce response times with guided remediation with continuous monitoring of your cloud infrastructure configurations by Sophos Cloud Optix.
Secure DevOps
Prevent security breaches pre-deployment by seamlessly integrating Sophos security and compliance checks with your CI/CD pipelines. Container image scanning and Infrastructure-as-Code (IaC) scanning in Sophos Cloud Optix stops threats into production environment.
Cloud Security Posture Management
Identify vulnerabilities, ensure compliance and respond to threats faster with Cloud Optix that detects insecure hosts, containers, and serverless deployments while monitoring configurations.
Cloud Access Control
Avoid over-privileged IAM roles and stolen cloud account credentials with Sophos AI that can pinpoint unusual access patterns and locations in near real time to identify credential theft.
Automate Threat Isolation and Cleanup
Sophos Synchronized Security enables your firewall and virtual machine security to automatically clean up malware, isolate infected workloads, and block lateral movement attempts.
Protect Cloud Data
Sophos Cloud Optix automatically detects and secures shared storage and database resources. Sophos Firewall identifies shadow IT in the cloud, alerting you of unauthorized behavior. Intercept X for Server stops ransomware while rolling back encrypted files and cleaning malicious code.
Synchronized Response
Get the world’s best cybersecurity system with Sophos Synchronized Security, where all Sophos products share information in real time and respond automatically to incidents to give you a unified, coordinated defense.
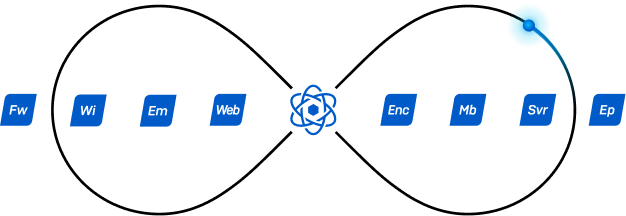
- Isolate infected endpoints, blocking lateral movement
- Restrict Wi-Fi for non-compliant mobile devices
- Scan endpoints on detection of compromised mailboxes
- Revoke encryption keys if a threat is detected
- Identify all apps on the network, and more
Take the Next Step
Tell us what you are looking for! Let our experts at Sophos help to build the right solution for your needs.