Extended Detection and Response (XDR)
Protect against sophisticated
multi-stage, multi-vector attacks
Sophos XDR provides powerful tools and threat intelligence that enable you to detect, investigate, and respond to suspicious activities across your entire IT ecosystem, delivered through Sophos’ adaptive AI-native, open platform.


A 2025 Gartner® Peer Insights™ “Customers’ Choice” for Extended Detection and Response
Protect against attacks that individual tools alone cannot stop.

Complex and evolving threat landscape

Data silos and blind spots
Disparate security tools operating in isolation create manual work for your team to correlate data, and blind spots that result in threats going unnoticed within your environment.

Increased workload and alert fatigue
Security teams are overwhelmed by a high volume of alerts from multiple tools, leading to analyst burnout and the potential for threats to be missed.

OVERVIEW
Stopping sophisticated attacks quickly is critical.



Increase ROI by integrating existing security and IT tools to detect and neutralize attacks.


Powerful tools and threat intelligence delivered through an AI-native, open platform.
Powerful threat detection, investigation, and response tools
AI-powered investigation and threat hunting
AI tools included with Sophos XDR streamline investigations by providing real-time insights, contextualizing threat data, and offering natural language-driven recommendations.
Prioritized detections
Easily identify suspicious activity that needs immediate attention. Sophos XDR automatically prioritizes detections across all key attack surfaces based on risk.
MITRE ATT&CK Framework mapping
Detections and cases are automatically mapped to MITRE ATT&CK Tactics, enabling you to identify gaps in your defenses.
Collaborative case management
Automatic case creation enables rapid investigation, with comprehensive case management tools for collaboration with team members.
Automated responses
Fully automated actions like process termination, ransomware rollback, network isolation, and adaptive attack protection, contain threats rapidly and save valuable time.
Analyst response actions
Your security analysts can execute an extensive range of response actions to contain and neutralize threats fast, including in Microsoft 365 environments, directly from the Sophos XDR platform.
Accelerate security operations with AI
Extensive GenAI capabilities in Sophos XDR empower your security analysts to neutralize adversaries faster, increasing both analyst and business confidence.
- AI Assistant makes it easy for users of all skill levels to get the information they need to progress threat investigations.
- AI Case Summary provides an easy-to-understand overview of detections, helping analysts make smart decisions, fast.
- AI Command Analysis delivers insights into attacker behavior by examining commands that create detections.
- AI Search and pre-canned query templates enable you to find the data you need faster, without needing to be an SQL expert.
Sophos AI Assistant
This isn't just another AI tool — it’s expertise from the team behind the world's leading Managed Detection and Response service, distilled into an intelligent agent.
- Conduct an extensive range of SecOps tasks: Analyze suspicious commands, identify impacted entities, enrich data with threat intelligence, create detailed reports, and more.
- Ask questions using everyday language or pre-defined prompts provided by Sophos’ threat experts. Benefit from natural language summaries and recommended next steps.
- Designed in partnership with Sophos’ frontline security analysts, enabling your in-house team to benefit from real-world workflows and the experience of Sophos MDR experts.
An open platform designed to optimize and unify.
Ingest and correlate data from multiple sources — choose the solutions you need from Sophos’ extensive portfolio or integrate your existing technology investments.
Sophos “XDR-ready” product integrations
Sophos solutions work together seamlessly to deliver the best-possible security outcomes. Our broad range of award-winning products, including Endpoint, Firewall, NDR, ZTNA, Email, Cloud, and Mobile, are fully integrated into the XDR platform — and the best-in-class protection of Sophos Endpoint is automatically included with your Sophos XDR subscription.
Non-Sophos technology integrations
Get more ROI from the security tools you use today by integrating them into our open platform. Sophos XDR includes turnkey integrations with an extensive ecosystem of third-party endpoint, firewall, network, email, identity, backup, cloud security, and productivity tools, including Microsoft 365 and Google Workspace.
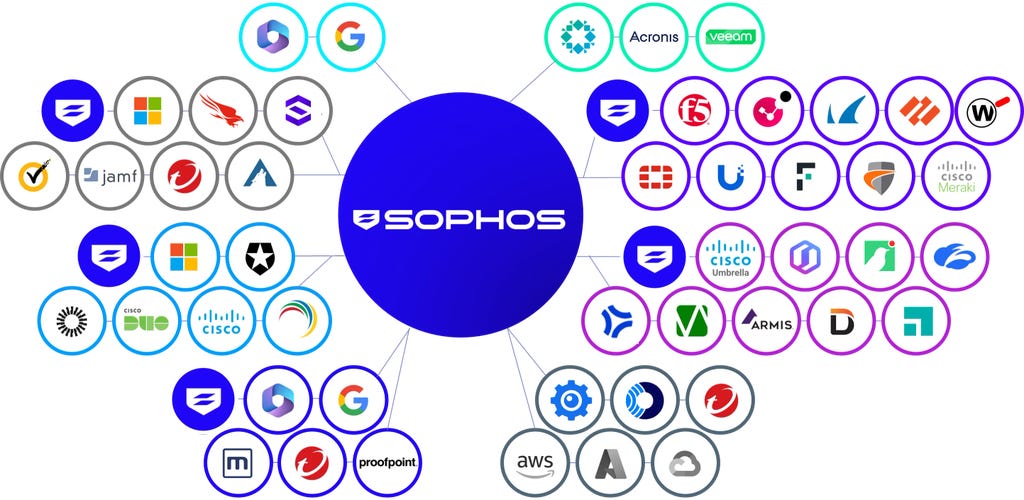
A representative sample of Sophos XDR technology integrations.
Sophos XDR attack simulation
See Sophos XDR in action, blocking threats and enabling analysts to quickly investigate and respond to suspicious activity using AI-powered tools and intuitive workflows.
In this attack simulation, detections generated by Sophos Endpoint, a non-Sophos firewall, and an email filtering platform, are automatically grouped into a single case by Sophos XDR for investigation and rapid remediation.
See why customers choose Sophos


The #1-rated XDR solution in the G2 Spring 2026 Reports

A 2026 Gartner® Peer Insights™ “Customers’ Choice” vendor for Extended Detection and Response (XDR).

A Leader in the IDC MarketScape: Worldwide Extended Detection and Response (XDR) Software 2025.
Sophos State of Ransomware 2025 Report
How likely are you to be hit by ransomware? How many of your computers would be affected? Find these answers and much more in the Sophos State of Ransomware 2025 Report.
RELATED PRODUCTS AND SERVICES
Cybersecurity for all your needs
Sophos Endpoint Detection and Response (EDR)
Sophos XDR includes Sophos EDR capabilities. Elevate your endpoint defenses with detection and response tools.
- Gain insights into evasive threats across your endpoints and servers.
- Includes powerful capabilities for IT operations and security analysts.
- Single agent for endpoint protection, detection, and response.
- Contain threats with accelerated and automated response tools.
- Multi-platform, multi-OS support.
Sophos Identity Threat Detection and Response (ITDR)
Sophos ITDR is an add-on for Sophos XDR, providing a holistic approach to reducing your organization's identity risk.
- Protect against advanced identity-based attacks.
- Identify misconfigurations and security gaps to reduce your attack surface.
- Uncover login credentials exposed on the dark web and breach databases.
- Accelerate your response to identity threats with analyst actions.
- Investigate abnormal activity associated with the use of stolen credentials.
Sophos Managed Detection and Response (MDR)
Free up IT and security staff and benefit from superior security outcomes delivered as a managed service by our highly skilled analysts.
- Instant security operations center (SOC).
- 24/7 threat detection and response.
- Proactive threat hunting.
- Full-scale incident response.
- Keep the cybersecurity software you already have.
- The most robust MDR service for Microsoft environments.
- Breach protection warranty.
Get started now

Explore the benefits of Sophos XDR.

Let us help find the right package for your business.

Get a no-obligation quote, customized to your needs.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)