As we reported on social media recently, Sophos X-Ops has been investigating reports of a fake Claude AI website distributing malware. Like other researchers, we thought this might be a PlugX-like campaign, given that the attack chain shares several characteristics with observed PlugX attacks.
However, on closer inspection we found something interesting: a first-stage DonutLoader payload, followed by what is, to our knowledge, a previously undocumented backdoor.
Je m’appelle Claude?
The malicious site (claude-pro[.]com) is similar in appearance to the legitimate Claude site, with similar fonts and colour palettes, although the fake version is noticeably simplistic, with only a handful of links – most of which redirect to the site’s front page.
Figure 1: The claude-pro[.]com front page
Interestingly, we suspect that the threat actor may have inadvertently disclosed their CloudFlare origin certificate, indicating a possible hosting server (209[.]189[.]190[.]206) which was set up in March 2026.
Even more interestingly, our research suggests another linked hosting server (178[.]128[.]108[.]89), associated with a domain called vertextrust-advisors[.]com. The site – registered in mid-April 2026 – purports to offer several services, including “Employment Lifecycle Compliance” and “Specialized Legal Advisory.” Bizarrely, the ‘About’ section states:
“Vertex Trust Advisors operates with physical precision. Our investigations begin with observations captured in offline, black Moleskine notebooks – a deliberate barrier against digital vulnerability. We employ ‘Penetration Investigation’ techniques to verify what data alone cannot. Upon project completion, all physical and digital traces are systematically eliminated via high-security German shredders.”

Figure 2: A website that may be linked to the threat actor behind claude-pro[.]com
We were unable to identify any other traces of this company, nor any binaries or files which could be downloaded from the site. It’s possible that this is part of a campaign still under construction.
The claude-pro[.]com site, however, is likely part of an active malvertising campaign. Malvertising is a common social engineering technique that tricks users into clicking malicious links in search engine results and/or prominently placed adverts. Typically threat actors achieve this by paying for malicious sites to appear as sponsored links, or by using SEO poisoning.
In this case, the site offers a ‘product’ called Claude-Pro Relay, via a download link. The file in question is Claude-Pro-windows-x64.zip, a large (approximately 505MB) archive.
Figure 3: The download link on the claude-pro[.]com site
This archive contains an MSI installer file (Claude.msi). Once executed, the installer drops three files into the user’s startup folder:
- NOVupdate.exe
- NOVupdate.exe.dat (an encrypted data file)
- avk.dll
As reported by MalwareBytes in their coverage of this attack, NOVupdate.exe appears to be a signed updater for G DATA antivirus products. When executed, it looks for avk.dll in its own directory. Here, the threat actor has used DLL sideloading, substituting the legitimate DLL for a malicious version.
As we’ve described in the past, DLL sideloading is a technique favoured by PlugX, a venerable malware family that we’ve been covering for 14 years. It’s by no means exclusive to PlugX; recent examples of threat actors using this method include Dragon Breath in May 2023 (featuring a double-sideloading attack), and GOLD BLADE in July 2025.
The use of a G DATA signed executable, a malicious, sideloaded version of avk.dll, and an encrypted data file, have previously been linked to PlugX, as noted by MalwareBytes – citing a February 2026 report by Lab52. Moreover, the use of three components – an executable, a DLL, and an encrypted data file – delivered in a compressed archive is also a common feature of PlugX campaigns.
That said, PlugX has multiple variants and has been associated with several threat actor groups, which complicates any attempt at attribution. Further muddying the water is the fact that ShadowPad – a backdoor that also employs DLL sideloading – shares numerous code overlaps with PlugX, to the extent that it may be considered an evolution of it.
Donut execute
The sideloaded DLL decrypts the encrypted payload in NOVupdate.exe.dat by reversing it and XORing it with the key SGkGIHumNrDlbt1OEHV3y2dVh5bQby2R (this is based on a hardcoded key, Qby2RSGkGIHumNrDlbt1OEHV3y2dVh5b; the decoding routine derives the key beginning at the fifth index of this string).
The malware then executes the decrypted shellcode using EtwpCreateEtwThread.
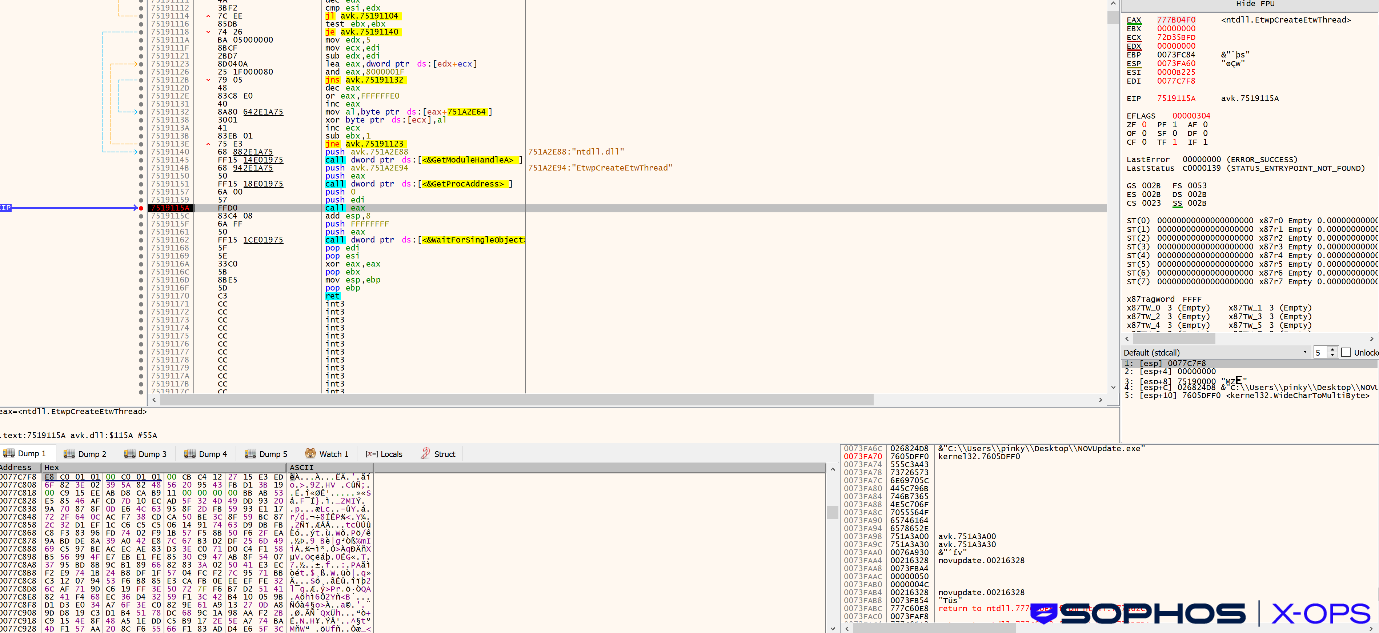
Figure 4: Decrypting and executing the first-stage shellcode
This decrypted payload is Donut (aka DonutLoader, aka donut_injector) shellcode – an open-source, in-memory loader. We’ve reported on Donut before – most notably, as part of our Crimson Palace investigation, relating to multiple attacks against government organizations in Southeast Asia.
The sequel: Beagle
Donut loads the final payload, which we assess to be a relatively simple backdoor with the following commands:
- uninstall: uninstalls agent
- cmd: executes command
- upload: uploads file
- download: downloads file
- mkdir: creates directory
- rename: renames file
- ls: lists directory content
- rm: removes directory
The backdoor communicates with the command-and-control (C2) server (license[.]claude-pro[.]com) over TCP (443) and/or UDP (8080). The IP address associated with this domain is 8[.]217[.]190[.]58.
The malware contains a hardcoded AES key (beagle_default_secret_key_12345!) and generates a 16-byte random IV every time it sends and receives a packet.
Via TCP, the packet structure is as follows (a 4-byte length parameter is included, due to the absence of packet length fields in TCP headers):
<4-byte length><16-byte random IV><AES-encrypted data>
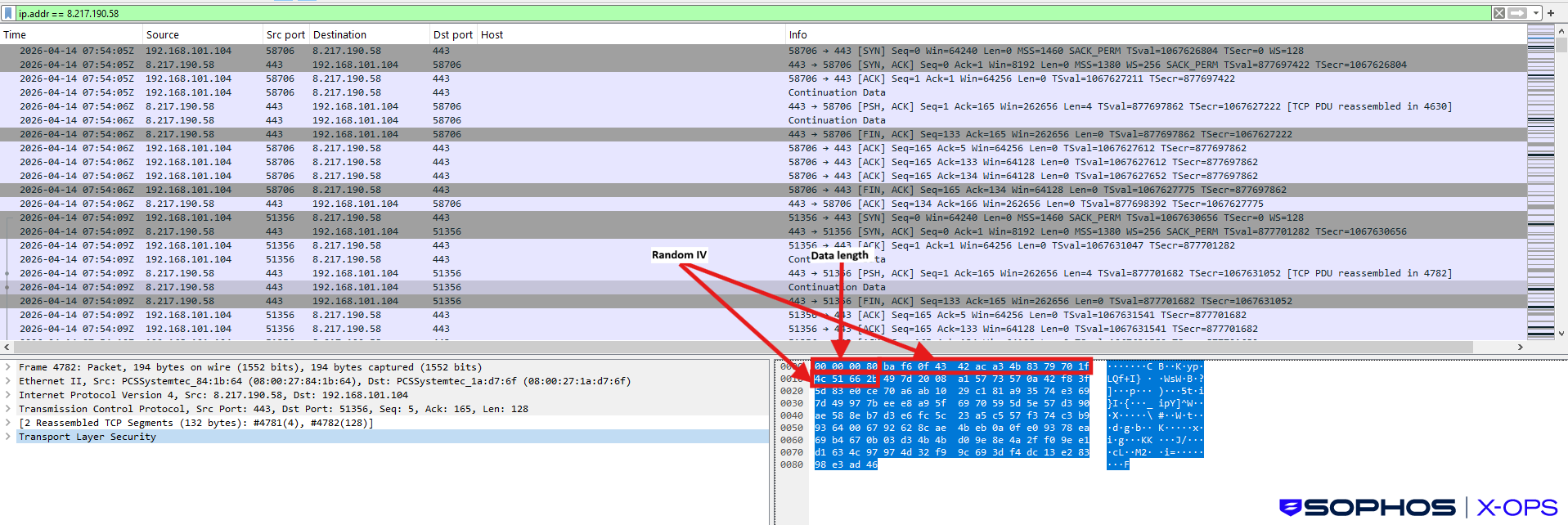
Figure 5: C2 communications over TCP
Communications over UDP are in the following format:
<16-byte random IV><AES-encrypted data>
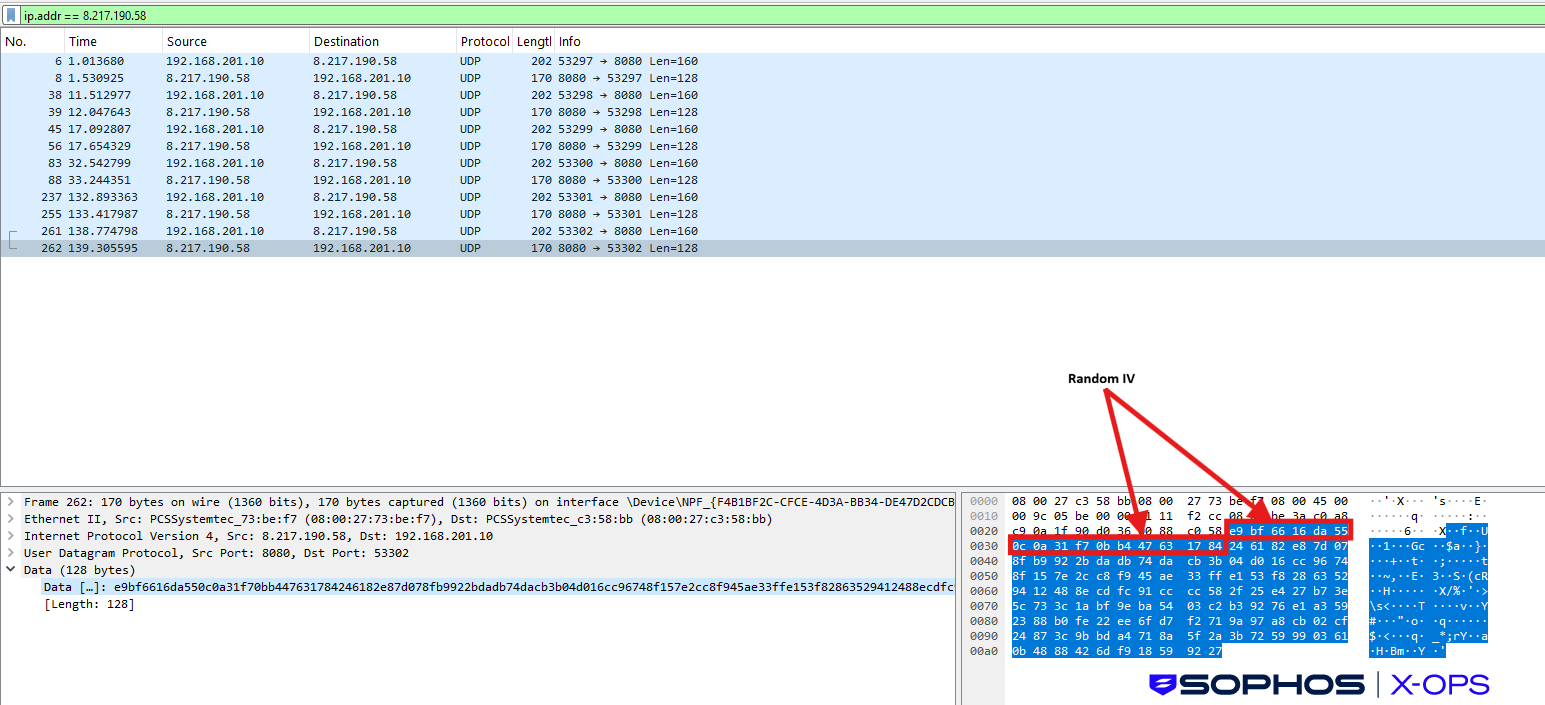
Figure 6: C2 communications over UDP
From the infected host to the C2 server, the structure of C2 communications is: {"type":10,"payload":"base64 content"} which decodes to {"agent_id":"agent-[id]","hostname":"","user":"","heartbeat":3}.
From C2 to victim, the structure is {"type":11,"payload":"base64 content"} which decodes to {"has_task":,"task":{"id":"","command":"","args":}}.
Note that ‘type 10’ therefore appears to indicate outgoing traffic (from victim to C2), whereas ‘type 11’ indicates incoming commands.
We were unable to find any public reporting about this backdoor, and have dubbed it ‘Beagle.’ (A note for older readers, this backdoor is not, to our knowledge,related to the Bagle/Beagle worm first observed in 2004).
Other samples
We found multiple other samples on VirusTotal that use the hardcoded XOR key noted above – one from February 2026, one from March, and two from April.
The February sample appears to be broadly similar to the one we investigated; it comprises what appears to be a legitimate file related to an antivirus/security solution (in this case, MpCopyAccelerator.exe, a Microsoft Defender utility) along with a malicious sideloaded DLL (MpClient.dll). This DLL is, like avk.dll in the described case, related to Donut. However, the encrypted data file (Windows.log in this sample) was not available, so we were unable to determine the C2 server.
The March sample is markedly different. While the infection chain once again features DLL sideloading, it also involves a decoy PDF file, and the decryption of a .log file culminating in the execution of AdaptixC2-related shellcode. (AdaptixC2 is an open-source red-teaming framework that we’ve seen used in ransomware attacks, specifically as part of a threat activity cluster we track as STAC4713, involving PayoutsKing ransomware). The C2 server used by this sample is gouvvbo[.]top.
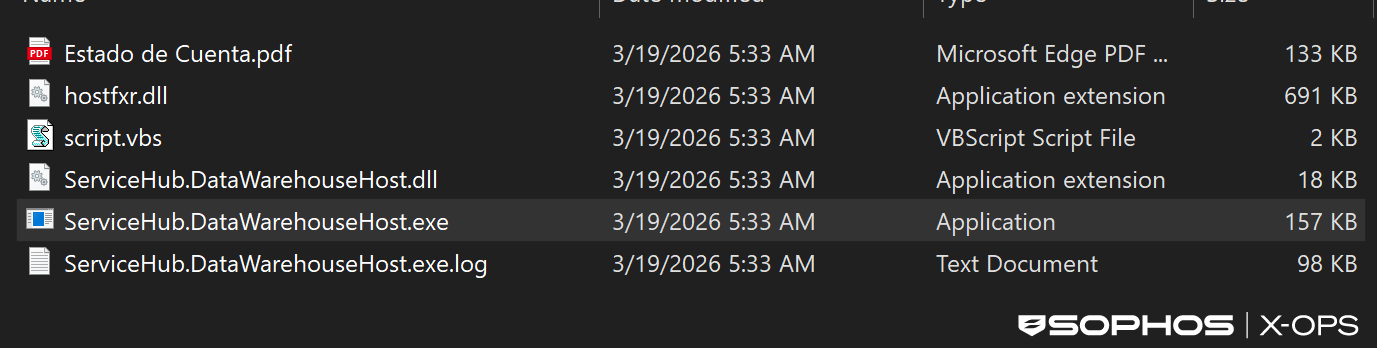
Figure 7: Files relating to the March 2026 sample
The first April sample appears to be broadly similar to the main sample we describe in this report. The archive name is Claude-Pro-Relay-Technical-Overview.zip, comprising NOVUpdate.exe, NOVUpdate.exe.dat, and avk.dll. The malware connects to licence[.]claude-pro[.]com.
The second (GolddTV.msi) is slightly different. It involves the same trio of filenames (albeit the sample contains two identical copies of each), but the payload (which we assess as a simple ‘connect-back’ shellcode, designed to download a next-stage shellcode payload) connects to update-trellix[.]com. Our research suggests that two other domains are hosted on the same IP (192[.]252[.]186[.]62): update-crowdstrike[.]com and update-sentinelone[.]com, potentially indicating a thematically-linked campaign or series of campaigns.
Implications
The use of a single parent domain for both malware distribution and C2, as in this case, is not unheard of, but is often seen in commodity campaigns – although it’s a somewhat weak signal for operator maturity.
In this case, we’ve seen reuse of the same XOR key across Donut samples from earlier in the year, along with anti-analysis methods, which could suggest some codebase continuity rather than a short-lived ‘smash-and-grab’ campaign. It’s also worth noting that while distribution and C2 sit under the same domain, the distribution was via Cloudflare, whereas the C2 was hosted on Alibaba Cloud – potentially to add some friction to disruption and takedown opportunities.
The website itself is a noteworthy aspect of this campaign. As we noted in a recent post on macOS infostealers, threat actors are clearly adapting to the widespread interest in popular AI tools, crafting lures that imitate legitimate AI sites (often as part of malvertising campaigns). The fake Claude site in this case was not a particularly sophisticated imitation; the fake website was relatively limited, and did not link back to the genuine site.
Most interestingly, previous reporting indicates that an almost identical sideloading chain, involving the use of G DATA artifacts, is associated with PlugX, but in this case, the eventual payload was a different backdoor. This may therefore be an example of a threat actor retooling (e.g., retaining the same infection chain, but swapping PlugX for an alternative), or imitating an infection chain used by another threat actor.
The presence of the same XOR key and varying infection chains and payloads in other samples could suggest threat actors tweaking and swapping tactics, techniques, and procedures (TTPs). However, it’s worth noting that while the XOR key may be relatively unique, further evidence would be required to conclude that these samples are linked to the same threat actor.
Protections
- Only download Claude from the legitimate site
- Be wary of following links from ads and sponsored search results
- Check system(s) for the files NOVupdate.exe, avk.dll, and NOVupdate.exe.dat (particularly in startup folders)
- This campaign’s infrastructure appears to be relatively static and limited. Monitor for connections to claude-pro[.]com and license[.]claude-pro[.]com (8[.]217[.]190[.]58)
Sophos has the following protections for the malicious components described in this article:
- ATK/DonutLdr-B
- Troj/Loader-OT
- Troj/Beagldr-A
- Troj/Loader-OX
- ATK/AdaptixC2-R
- Troj/LnkRun-EY
IOCs relating to this article are available on our GitHub repository.
Acknowledgments
Sophos X-Ops would like to thank Colin Cowie of Sophos’ Managed Detection and Response (MDR) team and Rafe Pilling of the Sophos Counter Threat Unit™ (CTU), for their contributions to this report.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)




