Microsoft on Tuesday released 84 patches affecting 15 product families – including a few you’ve possibly never encountered. Eight of the addressed issues are considered by Microsoft to be of Critical severity, though none of those affect Windows, nor are they expected to be exploited within the next 30 days. In addition, five of those Critical issues were in fact addressed by Microsoft in advance of Patch Tuesday itself, as we’ll discuss below. Twenty-two have a CVSS base score of 8.0 or higher, including one with a 9.8 base score. None are known to be under active exploit in the wild, but two are publicly disclosed so far.
At patch time, six CVEs are judged more likely to be exploited in the next 30 days by the company’s estimation. Various of this month’s issues are amenable to direct detection by Sophos protections, and we include information on those in the usual table below.
We are as always including at the end of this post appendices listing all Microsoft’s patches sorted by severity (Appendix A), by predicted exploitability timeline and CVSS Base score (Appendix B), and by product family (Appendix C). Appendix D lists ten Edge CVEs addressed this month, as well as three Adobe CVEs and one Critical-severity issue affecting Windows Sematic Kernel and expressed via GitHub. Appendix E provides a breakout of the 45 CVEs affecting various versions of Windows Server.
By the numbers
- Total CVEs: 84
- Publicly disclosed: 2
- Exploit detected: 0
- Severity
- Critical: 8
- Important: 76
- Impact:
- Denial of Service: 4
- Elevation of Privilege: 46
- Information Disclosure: 10
- Remote Code Execution: 17
- Security Feature Bypass: 3
- Spoofing: 4
- CVSS base score 9.0 or greater: 1
- CVSS base score 8.0 or greater: 22
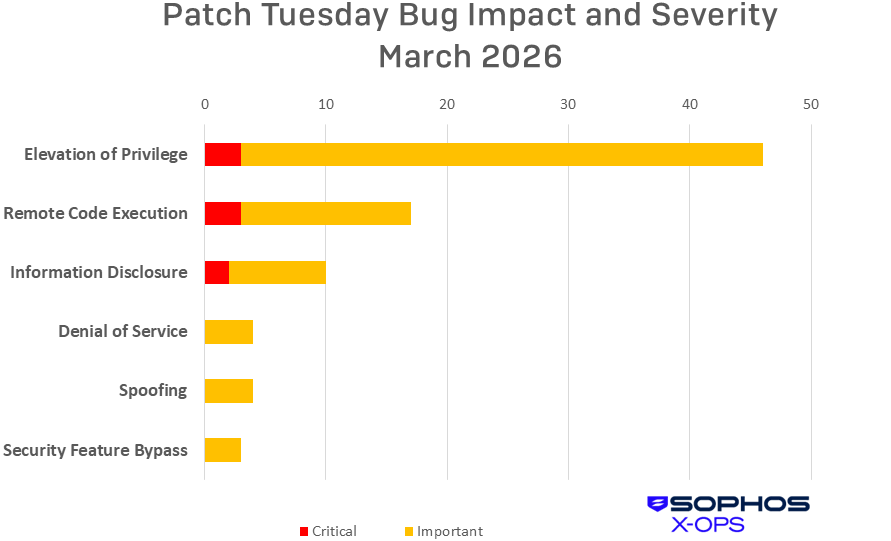
Figure 1: Elevation of Privilege issues once again lead the month by volume, though just three of those are Critical-severity
Products
As is our custom for this list, CVEs that apply to more than one product family are counted once for each family they affect. We note, by the way, that CVE names don’t always reflect affected product families closely. In particular, some CVEs names in the Office family may mention products that don’t appear in the list of products affected by the CVE, and vice versa.
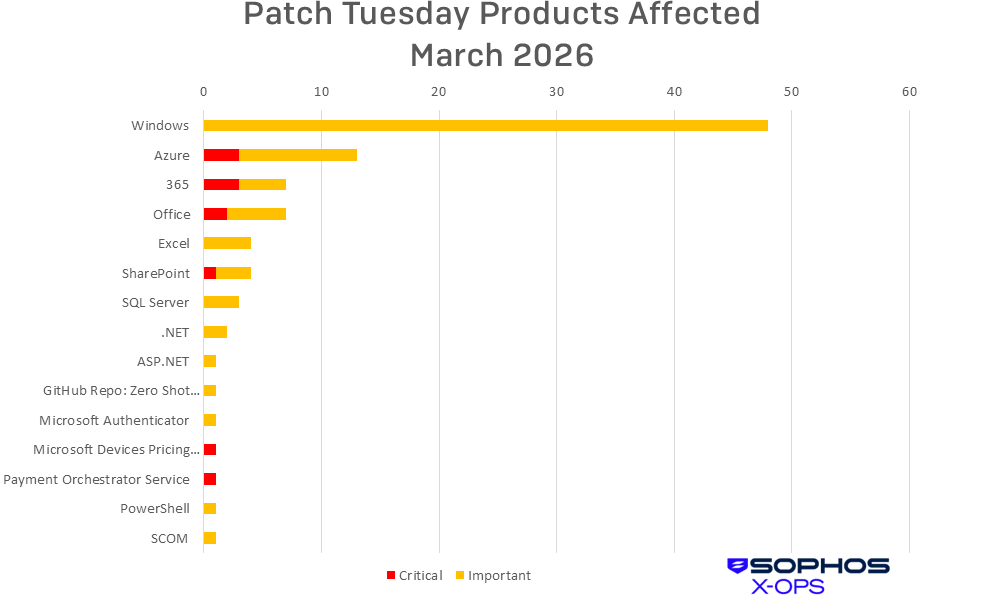
Figure 2: Windows bugs make up just over half the total number for March, but there’s a variety of relatively obscure product families affected by this month’s patches. The Microsoft Devices Pricing Program, familiar to Microsoft’s channel partners in particular, is discussed and the issue described here. The Payment Orchestrator Service platform and the issue patched are discussed here. Both are among the five Critical-severity bugs patched by Microsoft in advance of Patch Tuesday.
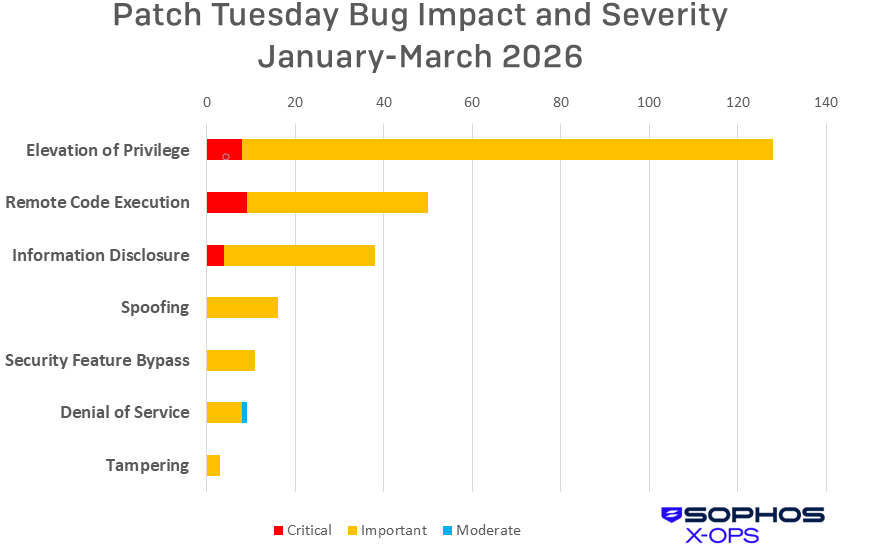
Figure 3: A quarter of the way through 2026, Elevation of Privilege issues constitute half of the 255 CVEs covered by Patch Tuesdays so far this year. Just 21 of the CVEs addressed in the normal course of patching have been of Critical severity
Notable March updates
In addition to the issues discussed above, a number of specific items merit attention.
CVE-2026-26110 -- Microsoft Office Remote Code Execution Vulnerability
CVE-2026-26113 -- Microsoft Office Remote Code Execution Vulnerability
CVE-2026-26144 -- Microsoft Excel Information Disclosure Vulnerability
As mentioned above, five of the eight Critical-severity CVEs patched this month were in fact handled before Patch Tuesday, with Microsoft simply providing information on those in the interests of transparency. These three, on the other hand, were not. The first two both list preview pane as a vector; both affect 365 and Office, and SharePoint is also listed for CVE-2026-26113. The remaining CVE, meanwhile, affects 365 but not Office (nor, according to Microsoft’s information, Excel specifically). According to Microsoft, an attacker who successfully exploited this vulnerability could potentially cause Copilot Agent mode to exfiltrate data via unintended network egress, enabling zero-click information disclosure attacks.
CVE-2026-23660 -- Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability
This Important-severity EoP requires some fairly specific administrator interaction, as there is no direct download link. Microsoft says, “Customers need to open the Extensions + Applications blade for their virtual machine in the Azure Portal and search for the extension named AdminCenter (Microsoft.AdminCenter.AdminCenter). From there, they can add or update the extension following the standard Azure VM extension installation process described here.”
CVE-2026-26123 -- Microsoft Authenticator Information Disclosure Vulnerability
This Important-severity information-disclosure issue requires some fairly specific user interaction. According to Microsoft, “the user must have a malicious application installed on their device and then accidentally select that application as the handler for the sign‑in deep link. This can occur when the user scans a QR code or taps a sign‑in link and chooses the malicious app instead of Microsoft Authenticator, causing the sign‑in flow to be handled by the attacker‑controlled app.” The issue affects both Android and iOS.
CVE-2026-24288 -- Windows Mobile Broadband Driver Remote Code Execution Vulnerability
The attack surface for this Important-severity RCE is a little perplexing – “triggered by physically connecting or manipulating hardware that interacts with the affected system” – until you notice that the finder, Nicolas Delhaye, is with aerospace titan Airbus. So… did you plug your phone into the seatback charger on your last flight?
CVE-2026-21262 – SQL Server Elevation of Privilege Vulnerability
This Important-severity bug, one of two that has already been publicly disclosed, came to Microsoft through one of the longest-tenured members of one of the longest-tenured outreach programs at the Redmond company. Erland Sommarskog with Erland Sommarskog SQL-Konsult AB, who has been a Microsoft MVP for twenty-five years, scores a finder credit for this one.
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
|---|---|---|
| CVE-2026-24289 | Exp/2624289-A | Exp/2624289-A |
| CVE-2026-24291 | Exp/2624291-A | Exp/2624291-A |
| CVE-2026-25187 | Exp/2625187-A | Exp/2625187-A |
| CVE-2026-26132 | Exp/2626132-A | Exp/2626132-A |
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of March patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Elevation of Privilege (46 CVEs)
| Critical severity | |
| CVE-2026-23651 | Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability |
| CVE-2026-26124 | Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability |
| CVE-2026-26125 | Payment Orchestrator Service Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2026-23651 | System Center Operations Manager (SCOM) Elevation of Privilege Vulnerability |
| CVE-2026-26124 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-26125 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability |
| CVE-2026-20967 | Linux Azure Diagnostic extension (LAD) Elevation of Privilege Vulnerability |
| CVE-2026-21262 | Broadcast DVR Elevation of Privilege Vulnerability |
| CVE-2026-23660 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2026-23665 | Windows Bluetooth RFCOM Protocol Driver Elevation of Privilege Vulnerability |
| CVE-2026-23667 | Windows Universal Disk Format File System Driver (UDFS) Elevation of Privilege Vulnerability |
| CVE-2026-23668 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability |
| CVE-2026-23671 | Multiple UNC Provider Kernel Driver Elevation of Privilege Vulnerability |
| CVE-2026-23672 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-23673 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-24283 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-24285 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-24287 | Windows Accessibility Infrastructure (ATBroker.exe) Elevation of Privilege Vulnerability |
| CVE-2026-24289 | Windows Connected Devices Platform Service Elevation of Privilege Vulnerability |
| CVE-2026-24290 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-24291 | Windows SMB Server Elevation of Privilege Vulnerability |
| CVE-2026-24292 | Windows Device Association Service Elevation of Privilege Vulnerability |
| CVE-2026-24293 | Windows Device Association Service Elevation of Privilege Vulnerability |
| CVE-2026-24294 | Performance Counters for Windows Elevation of Privilege Vulnerability |
| CVE-2026-24295 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-24296 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2026-25165 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2026-25167 | Windows Extensible File Allocation Table Elevation of Privilege Vulnerability |
| CVE-2026-25170 | Windows NTFS Elevation of Privilege Vulnerability |
| CVE-2026-25171 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-25174 | Active Directory Domain Services Elevation of Privilege Vulnerability |
| CVE-2026-25175 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-25176 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-25177 | Winlogon Elevation of Privilege Vulnerability |
| CVE-2026-25178 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-25179 | Windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2026-25187 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-25188 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-25189 | Arc Enabled Servers - Azure Connected Machine Agent Elevation of Privilege Vulnerability |
| CVE-2026-26115 | Azure MCP Server Tools Elevation of Privilege Vulnerability |
| CVE-2026-26116 | Windows SMB Server Elevation of Privilege Vulnerability |
| CVE-2026-26117 | .NET Elevation of Privilege Vulnerability |
| CVE-2026-26118 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26128 | Microsoft Office Elevation of Privilege Vulnerability |
| CVE-2026-26131 | Hybrid Worker Extension (Arc‑enabled Windows VMs) Elevation of Privilege Vulnerability |
| CVE-2026-26132 | Microsoft Azure AD SSH Login extension for Linux Elevation of Privilege Vulnerability |
Remote Code Execution (14 CVEs)
| Critical severity | |
| CVE-2026-21536 | Microsoft Devices Pricing Program Remote Code Execution Vulnerability |
| CVE-2026-26110 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-23654 | GitHub: Zero Shot SCFoundation Remote Code Execution Vulnerability |
| CVE-2026-23669 | Windows Print Spooler Remote Code Execution Vulnerability |
| CVE-2026-24288 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability |
| CVE-2026-25166 | Windows System Image Manager Assessment and Deployment Kit (ADK) Remote Code Execution Vulnerability |
| CVE-2026-25172 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2026-25173 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2026-25190 | GDI Remote Code Execution Vulnerability |
| CVE-2026-26106 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-26107 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26108 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26109 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26111 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2026-26112 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26114 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Information Disclosure (10 CVEs)
| Critical severity | |
| CVE-2026-26122 | Microsoft ACI Confidential Containers Information Disclosure Vulnerability |
| CVE-2026-26144 | Microsoft Excel Information Disclosure Vulnerability |
| Important severity | |
| CVE-2026-23661 | Azure IoT Explorer Information Disclosure Vulnerability |
| CVE-2026-23662 | Azure IoT Explorer Information Disclosure Vulnerability |
| CVE-2026-23664 | Azure IoT Explorer Information Disclosure Vulnerability |
| CVE-2026-24282 | Push message Routing Service Elevation of Privilege Vulnerability |
| CVE-2026-25180 | Windows Graphics Component Information Disclosure Vulnerability |
| CVE-2026-25181 | GDI+ Information Disclosure Vulnerability |
| CVE-2026-25186 | Windows Accessibility Infrastructure (ATBroker.exe) Information Disclosure Vulnerability |
| CVE-2026-26123 | Microsoft Authenticator Information Disclosure Vulnerability |
Denial of Service (4 CVEs)
| Important severity | |
| CVE-2026-25168 | Windows Graphics Component Denial of Service Vulnerability |
| CVE-2026-25169 | Windows Graphics Component Denial of Service Vulnerability |
| CVE-2026-26127 | .NET Denial of Service Vulnerability |
| CVE-2026-26130 | ASP.NET Core Denial of Service Vulnerability |
Spoofing (4 CVEs)
| Important severity | |
| CVE-2026-23656 | Windows App Installer Spoofing Vulnerability |
| CVE-2026-25185 | Windows Shell Link Processing Spoofing Vulnerability |
| CVE-2026-26105 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2026-26121 | Azure IOT Explorer Spoofing Vulnerability |
Security Feature Bypass (3 CVEs)
| Important severity | |
| CVE-2026-23674 | MapUrlToZone Security Feature Bypass Vulnerability |
| CVE-2026-24297 | Windows Kerberos Security Feature Bypass Vulnerability |
| CVE-2026-26143 | Microsoft PowerShell Security Feature Bypass Vulnerability |
Appendix B: Exploitability and CVSS
This is a list of the six March CVEs judged by Microsoft to be more likely to be exploited in the wild within the first 30 days post-release. The list is arranged by CVE.
| Exploitation more likely within the next 30 days | |
| CVE-2026-23668 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2026-24289 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-24291 | Windows Accessibility Infrastructure (ATBroker.exe) Elevation of Privilege Vulnerability |
| CVE-2026-24294 | Windows SMB Server Elevation of Privilege Vulnerability |
| CVE-2026-25187 | Winlogon Elevation of Privilege Vulnerability |
| CVE-2026-26132 | Windows Kernel Elevation of Privilege Vulnerability |
These are the March CVEs with a Microsoft-assessed CVSS Base score of 8.0 or higher. They are arranged by score and further sorted by CVE. For more information on how CVSS works, please see our series on patch prioritization schema.
| CVSS Base | CVSS Temporal | CVE | Title |
| 9.8 | 8.5 | CVE-2026-21536 | Microsoft Devices Pricing Program Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-20967 | System Center Operations Manager (SCOM) Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-21262 | SQL Server Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-23654 | GitHub: Zero Shot SCFoundation Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-23669 | Windows Print Spooler Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-24283 | Multiple UNC Provider Kernel Driver Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-25172 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-25177 | Active Directory Domain Services Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-25188 | Windows Telephony Service Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-26106 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-26111 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-26114 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-26115 | SQL Server Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-26116 | SQL Server Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-26118 | Azure MCP Server Tools Elevation of Privilege Vulnerability |
| 8.6 | 7.7 | CVE-2026-26125 | Payment Orchestrator Service Elevation of Privilege Vulnerability |
| 8.4 | 7.3 | CVE-2026-26109 | Microsoft Excel Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-26110 | Microsoft Office Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability |
| 8.1 | 7.1 | CVE-2026-26105 | Microsoft SharePoint Server Spoofing Vulnerability |
| 8.1 | 7.3 | CVE-2026-26148 | Microsoft Azure AD SSH Login extension for Linux Elevation of Privilege Vulnerability |
| 8.0 | 7.0 | CVE-2026-25173 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
Appendix C: Products Affected
This is a list of March’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple times, once for each product family. Certain issues for which advisories have been issued are covered in Appendix D, and issues affecting Windows Server are further sorted in Appendix E. All CVE titles are accurate as made available by Microsoft; for further information on why certain products may appear in titles and not product families (or vice versa), please consult Microsoft.
Windows (48 CVEs)
| Important severity | |
| CVE-2026-23656 | Windows App Installer Spoofing Vulnerability |
| CVE-2026-23667 | Broadcast DVR Elevation of Privilege Vulnerability |
| CVE-2026-23668 | Windows Graphics Component Elevation of Privilege Vulnerability |
| CVE-2026-23669 | Windows Print Spooler Remote Code Execution Vulnerability |
| CVE-2026-23671 | Windows Bluetooth RFCOM Protocol Driver Elevation of Privilege Vulnerability |
| CVE-2026-23672 | Windows Universal Disk Format File System Driver (UDFS) Elevation of Privilege Vulnerability |
| CVE-2026-23673 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability |
| CVE-2026-23674 | MapUrlToZone Security Feature Bypass Vulnerability |
| CVE-2026-24282 | Push message Routing Service Elevation of Privilege Vulnerability |
| CVE-2026-24283 | Multiple UNC Provider Kernel Driver Elevation of Privilege Vulnerability |
| CVE-2026-24285 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-24287 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-24288 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability |
| CVE-2026-24289 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-24290 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-24291 | Windows Accessibility Infrastructure (ATBroker.exe) Elevation of Privilege Vulnerability |
| CVE-2026-24292 | Windows Connected Devices Platform Service Elevation of Privilege Vulnerability |
| CVE-2026-24293 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-24294 | Windows SMB Server Elevation of Privilege Vulnerability |
| CVE-2026-24295 | Windows Device Association Service Elevation of Privilege Vulnerability |
| CVE-2026-24296 | Windows Device Association Service Elevation of Privilege Vulnerability |
| CVE-2026-24297 | Windows Kerberos Security Feature Bypass Vulnerability |
| CVE-2026-25165 | Performance Counters for Windows Elevation of Privilege Vulnerability |
| CVE-2026-25166 | Windows System Image Manager Assessment and Deployment Kit (ADK) Remote Code Execution Vulnerability |
| CVE-2026-25167 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-25168 | Windows Graphics Component Denial of Service Vulnerability |
| CVE-2026-25169 | Windows Graphics Component Denial of Service Vulnerability |
| CVE-2026-25170 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2026-25171 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2026-25172 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2026-25173 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2026-25174 | Windows Extensible File Allocation Table Elevation of Privilege Vulnerability |
| CVE-2026-25175 | Windows NTFS Elevation of Privilege Vulnerability |
| CVE-2026-25176 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-25177 | Active Directory Domain Services Elevation of Privilege Vulnerability |
| CVE-2026-25178 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-25179 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-25180 | Windows Graphics Component Information Disclosure Vulnerability |
| CVE-2026-25181 | GDI+ Information Disclosure Vulnerability |
| CVE-2026-25185 | Windows Shell Link Processing Spoofing Vulnerability |
| CVE-2026-25186 | Windows Accessibility Infrastructure (ATBroker.exe) Information Disclosure Vulnerability |
| CVE-2026-25187 | Winlogon Elevation of Privilege Vulnerability |
| CVE-2026-25188 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-25189 | Windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2026-25190 | GDI Remote Code Execution Vulnerability |
| CVE-2026-26111 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2026-26128 | Windows SMB Server Elevation of Privilege Vulnerability |
| CVE-2026-26132 | Windows Kernel Elevation of Privilege Vulnerability |
Azure (13 CVEs)
| Critical severity | |
| CVE-2026-23651 | Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability |
| CVE-2026-26122 | Microsoft ACI Confidential Containers Information Disclosure Vulnerability |
| CVE-2026-26124 | Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2026-23660 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability |
| CVE-2026-23661 | Azure IoT Explorer Information Disclosure Vulnerability |
| CVE-2026-23662 | Azure IoT Explorer Information Disclosure Vulnerability |
| CVE-2026-23664 | Azure IoT Explorer Information Disclosure Vulnerability |
| CVE-2026-23665 | Linux Azure Diagnostic extension (LAD) Elevation of Privilege Vulnerability |
| CVE-2026-26117 | Arc Enabled Servers - Azure Connected Machine Agent Elevation of Privilege Vulnerability |
| CVE-2026-26118 | Azure MCP Server Tools Elevation of Privilege Vulnerability |
| CVE-2026-26121 | Azure IOT Explorer Spoofing Vulnerability |
| CVE-2026-26141 | Hybrid Worker Extension (Arc‑enabled Windows VMs) Elevation of Privilege Vulnerability |
| CVE-2026-26148 | Microsoft Azure AD SSH Login extension for Linux Elevation of Privilege Vulnerability |
365 (7 CVEs)
| Critical severity | |
| CVE-2026-26110 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-26144 | Microsoft Excel Information Disclosure Vulnerability |
| Important severity | |
| CVE-2026-26107 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26108 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26109 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26112 | Microsoft Excel Remote Code Execution Vulnerability |
Office (7 CVEs)
| Critical severity | |
| CVE-2026-26110 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-26107 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26108 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26109 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26112 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26134 | Microsoft Office Elevation of Privilege Vulnerability |
Excel (4 CVEs)
| Important severity | |
| CVE-2026-26107 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26108 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26109 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-26112 | Microsoft Excel Remote Code Execution Vulnerability |
SharePoint (3 CVEs)
| Critical severity | |
| CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-26105 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2026-26106 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-26114 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
SQL Server (2 CVEs)
| Important severity | |
| CVE-2026-21262 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-26115 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-26116 | SQL Server Elevation of Privilege Vulnerability |
NET (2 CVEs)
| Important severity | |
| CVE-2026-26127 | .NET Denial of Service Vulnerability |
| CVE-2026-26131 | .NET Elevation of Privilege Vulnerability |
ASP.NET (1 CVE)
| Important severity | |
| CVE-2026-26130 | ASP.NET Core Denial of Service Vulnerability |
GitHub Repo: Zero Shot scFoundation (1 CVE)
| Important severity | |
| CVE-2026-23654 | GitHub: Zero Shot SCFoundation Remote Code Execution Vulnerability |
Microsoft Authenticator (1 CVE)
| Important severity | |
| CVE-2026-26123 | Microsoft Authenticator Information Disclosure Vulnerability |
Microsoft Devices Pricing Program (1 CVE)
| Critical severity | |
| CVE-2026-21536 | Microsoft Devices Pricing Program Remote Code Execution Vulnerability |
Payment Orchestrator Service (1 CVE)
| Critical severity | |
| CVE-2026-26125 | Payment Orchestrator Service Elevation of Privilege Vulnerability |
PowerShell (1 CVE)
| Important severity | |
| CVE-2026-26143 | Microsoft PowerShell Security Feature Bypass Vulnerability |
System Center Operations Manager (SCOM) (1 CVE)
| Important severity | |
| CVE-2026-20967 | System Center Operations Manager (SCOM) Elevation of Privilege Vulnerability |
Appendix D: Advisories and Other Products
March includes a CVE concerning an Important-severity RCE bug in Microsoft Semantic Kernel that rates a lofty 9.9 Base CVSS, though Microsoft judges that exploitation of the issue is unlikely within the next 30 days. There is a listed mitigation for this issue, which is to avoid using InMemoryVectorStore for production scenarios.
| CVE-2026-26030 | GitHub: CVE-2026-26030 Microsoft Semantic Kernel InMemoryVectorStore filter functionality vulnerable |
There are also ten Edge-related advisories listed in March’s release; all but CVE-2026-26140 were patched prior to Tuesday’s release. All but CVE-2026-3545 are marked in Microsoft’s information as unlikely to be exploited within the next 30 days.
| CVE-2026-3536 | Chromium: CVE-2026-3536 Integer overflow in ANGLE |
| CVE-2026-3538 | Chromium: CVE-2026-3538 Integer overflow in Skia |
| CVE-2026-3539 | Chromium: CVE-2026-3539 Object lifecycle issue in DevTools |
| CVE-2026-3540 | Chromium: CVE-2026-3540 Inappropriate implementation in WebAudio |
| CVE-2026-3541 | Chromium: CVE-2026-3541 Inappropriate implementation in CSS |
| CVE-2026-3542 | Chromium: CVE-2026-3542 Inappropriate implementation in WebAssembly |
| CVE-2026-3543 | Chromium: CVE-2026-3543 Inappropriate implementation in V8 |
| CVE-2026-3544 | Chromium: CVE-2026-3544 Heap buffer overflow in WebCodecs |
| CVE-2026-3545 | Chromium: CVE-2026-3545 Insufficient data validation in Navigation |
| CVE-2026-26140 | Microsoft Edge (Chromium-based) Spoofing Vulnerability |
Finally, there are three updates from Adobe, all affecting Reader 25.001.20982, 24.001.30264 (Windows), 24.001.30273 (Mac) and earlier; they are addresseḍ in APSB26-26.
| CVE-2026-27220 | Use After Free (CWE-416) |
| CVE-2026-27221 | Improper Verification of Cryptographic Signature (CWE-347) |
| CVE-2026-27278 | Use After Free (CWE-416) |
Appendix E: Affected Windows Server versions
This is a table of the 45 CVEs in the March release affecting Windows Server versions 2012 through 2025. The table differentiates among major versions of the platform but doesn’t go into deeper detail (eg., Server Core). An “x” indicates that the CVE does not apply to that version. CVE-2026-23667, CVE-2026-24282, and CVE-2026-24288 affect only client-side versions of Windows and are thus not included in the table.
Administrators are encouraged to use this appendix as a starting point to ascertain their specific exposure, as each reader’s situation, especially as it concerns products out of mainstream support, will vary. For specific Knowledge Base numbers, please consult Microsoft.
| CVE | S-12 | 12r2 | S-16 | S-19 | S-22 | 23h2 | S-25 |
|---|---|---|---|---|---|---|---|
| CVE-2026-23656 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-23668 | ■ | ■ | ■ | ■ | ■ | ■ | × |
| CVE-2026-23669 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-23671 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-23672 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-23673 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-23674 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24283 | × | × | × | × | × | ■ | ■ |
| CVE-2026-24285 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24287 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-24289 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24290 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-24291 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24292 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-24293 | × | × | × | × | ■ | ■ | ■ |
| CVE-2026-24294 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24295 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24296 | × | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-24297 | ■ | ■ | ■ | ■ | × | × | × |
| CVE-2026-25165 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25166 | × | × | ■ | ■ | ■ | ■ | × |
| CVE-2026-25167 | × | × | × | × | × | × | ■ |
| CVE-2026-25168 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25169 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25170 | × | × | × | × | ■ | ■ | ■ |
| CVE-2026-25171 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25172 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25173 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25174 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25175 | ■ | ■ | ■ | ■ | ■ | ■ | × |
| CVE-2026-25176 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25177 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25178 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25179 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25180 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25181 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25185 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25186 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25187 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25188 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-25189 | × | × | × | ■ | ■ | × | × |
| CVE-2026-25190 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-26111 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-26128 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-26132 | × | × | × | × | ■ | ■ | ■ |
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


