In another banner month for the AI-finder era, Microsoft on Tuesday released 132 patches affecting 20 product families. Twenty-nine of the addressed issues are considered by Microsoft to be of Critical severity, and 13 issues are expected to be exploited within the next 30 days. Forty-three have a CVSS base score of 8.0 or higher, including one with a “perfect” 10.0. Fourteen CVEs, including the 10.0 item mentioned above, were patched by Microsoft in advance of Patch Tuesday. Incredibly, none were publicly disclosed as of release day and none are known to be under active exploit in the wild.
For the second month in a row, the release includes massive set of advisories – 145 of them. As ever, the majority are Edge-related, assigned by Chrome, and patched days in advance of Patch Tuesday. One comes from AMD and was likewise already addressed. Thirteen, all affecting Adobe Commerce, were issued by Adobe.
Various of this month’s issues are amenable to direct detection by Sophos protections, and we include information on those in the usual table below. We are as always including at the end of this post appendices listing all Microsoft’s patches sorted by severity (Appendix A), by predicted exploitability timeline and CVSS Base score (Appendix B), and by product family (Appendix C). Appendix D lists this month’s advisories. Appendix E provides a breakout of 66 CVEs affecting various versions of Windows Server, including the advisory from AMD that is otherwise not counted in the patch totals for the month. Our analysis of CWE (Common Weakness Enumeration) information made available for this month’s patches appears in Appendix F.
By the numbers
- Total CVEs: 132
- Publicly disclosed: 0
- Exploit detected: 0
- Severity
- Critical: 29
- Important: 103
- Impact:
- Denial of Service: 8
- Elevation of Privilege: 59
- Information Disclosure: 14
- Remote Code Execution: 31
- Security Feature Bypass: 6
- Spoofing: 11
- Tampering: 3
- CVSS base score 9.0 or greater: 14
- CVSS base score 8.0 or greater: 43
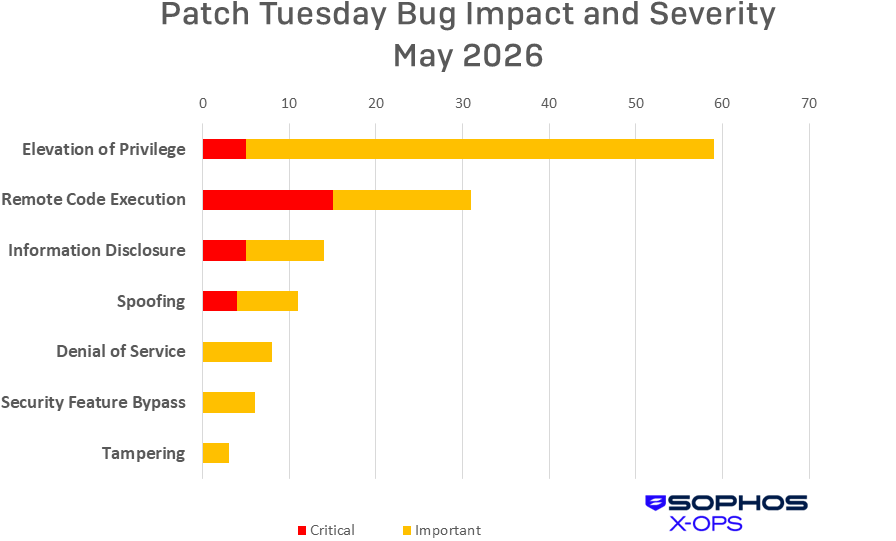
Figure 1: Elevation of Privilege issues once again account for the majority of the month’s CVEs, but nearly half of the Remote Control Execution CVEs are Critical-severity.
Products
As is our custom for this list, CVEs that apply to more than one product family are counted once for each family they affect. We note, by the way, that CVE names don’t always reflect affected product families closely. In particular, some CVEs names in the Office family may mention products that don’t appear in the list of products affected by the CVE, and vice versa.
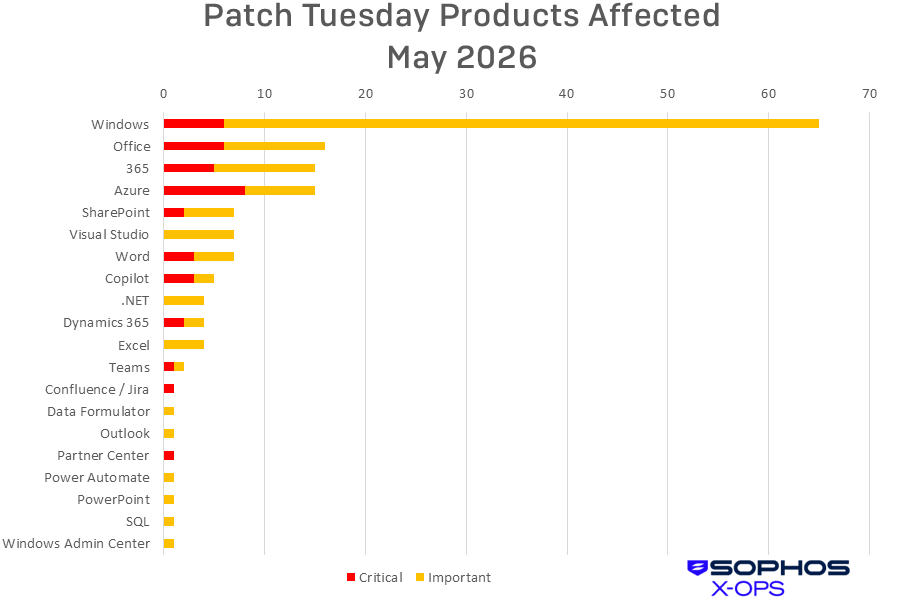
Figure 2: A hefty 20 families are covered in May’s Patch Tuesday release. The Critical-severity issue called “Confluence / Jira” covers an SSO plug-in for those tools, as described below.
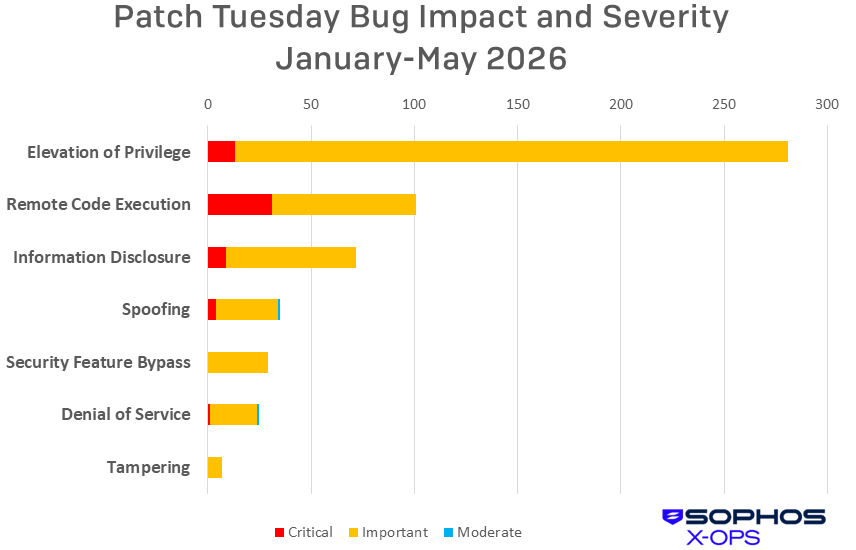
Figure 3: The count of Elevation of Privilege CVEs passes 250, and Spoofing and Security Feature Bypass swap spots on the cumulative list of 2026 vulnerabilities. By way of comparison, as of this time last year Microsoft had addressed 470 CVEs.
Notable May updates
In addition to the issues discussed above, a few specific items merit attention.
CVE-2026-41103 -- Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability
There are 14 CVEs with a CVSS Base score of 9.0 or higher this month (with 11 of those also marked as Critical-severity), but the only one Microsoft thinks is more likely to be exploited in the next 30 days is this Critical-severity Elevation of Privilege issue, which involves an incorrect implementation of an authentication algorithm (CWE-303) – not far-fetched, since this involves SSO. The bug would permit an attacker to bypass authentication and sign in as a valid user. The specifically affected plug-ins are the Microsoft Confluence SAML SSO plugin and the Microsoft JIRA SAML SSO plugin.
CVE-2026-41089 -- Windows Netlogon Remote Code Execution Vulnerability
CVE-2026-41096 -- Windows DNS Client Remote Code Execution Vulnerability
Also in the over-9.0 CVSS Club with matching base scores of 9.8, these two CVEs both allow exploitation even by an unauthorized attacker.
CVE-2026-40358 -- Microsoft Office Remote Code Execution Vulnerability
CVE-2026-40361 -- Microsoft Word Remote Code Execution Vulnerability
CVE-2026-40363 -- Microsoft Office Remote Code Execution Vulnerability
CVE-2026-40364 -- Microsoft Word Remote Code Execution Vulnerability
CVE-2026-40366 -- Microsoft Word Remote Code Execution Vulnerability
CVE-2026-40367 – Microsoft Word Remote Code Execution Vulnerability
All six of these Remote Code Execution vulnerabilities can be exploited via Preview Pane. Of the six, CVE-2026-40361 and CVE-2026-40364 are thought by Microsoft to be more likely to be exploited within the first 30 days post-release.
CVE-2026-35432 -- Windows 11 Telnet Client Information Disclosure Vulnerability
Telnet. That is all. Yes, it’s still 2026.
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2026-33835 | Exp/2633835-A | Exp/2633835-A |
| CVE-2026-33837 | Exp/2633837-A | Exp/2633837-A |
| CVE-2026-33840 | Exp/2633840-A | Exp/2633840-A |
| CVE-2026-33841 | Exp/2633841-A | Exp/2633841-A |
| CVE-2026-35416 | Exp/2635416-A | Exp/2635416-A |
| CVE-2026-35417 | Exp/2635417-A | Exp/2635417-A |
| CVE-2026-40361 | sid:2312491, sid:2312492 | sid:2312491, sid:2312492 |
| CVE-2026-40364 | sid:2312493, sid:2312494 | sid:2312493, sid:2312494 |
| CVE-2026-40369 | Exp/2640369-A | Exp/2640369-A |
| CVE-2026-40397 | Exp/2640397-A | Exp/2640397-A |
| CVE-2026-40398 | Exp/2640398-A | Exp/2640398-A |
| CVE-2026-41089 | sid:2312495 | sid:2312495 |
| CVE-2026-41103 | sid:2312499 | sid:2312499 |
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of May patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Elevation of Privilege (59 CVEs)
| Critical severity | |
| CVE-2026-33821 | Microsoft Dynamics 365 Customer Insights Elevation of Privilege Vulnerability |
| CVE-2026-35435 | Azure AI Foundry Elevation of Privilege Vulnerability |
| CVE-2026-40402 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability |
| CVE-2026-41105 | Azure Monitor Action Group Notification System Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2026-21530 | Windows Rich Text Edit Elevation of Privilege Vulnerability |
| CVE-2026-32170 | Windows Rich Text Edit Elevation of Privilege Vulnerability |
| CVE-2026-32177 | .NET Elevation of Privilege Vulnerability |
| CVE-2026-32204 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2026-33834 | Windows Event Logging Service Elevation of Privilege Vulnerability |
| CVE-2026-33835 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-33837 | Windows TCP/IP Local Elevation of Privilege Vulnerability |
| CVE-2026-33838 | Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2026-33839 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33840 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33841 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-34330 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34331 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34333 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34334 | Windows TCP/IP Elevation of Privilege Vulnerability |
| CVE-2026-34337 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-34338 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-34340 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-34341 | Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability |
| CVE-2026-34342 | Windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2026-34343 | Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability |
| CVE-2026-34344 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-34345 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-34347 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34351 | Windows TCP/IP Elevation of Privilege Vulnerability |
| CVE-2026-35415 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability |
| CVE-2026-35416 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-35417 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-35418 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-35420 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-35433 | .NET Elevation of Privilege Vulnerability |
| CVE-2026-35436 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-35438 | Windows Admin Center Elevation of Privilege Vulnerability |
| CVE-2026-40369 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-40377 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability |
| CVE-2026-40381 | Azure Connected Machine Agent Elevation of Privilege Vulnerability |
| CVE-2026-40382 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-40397 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-40398 | Windows Remote Desktop Services Elevation of Privilege Vulnerability |
| CVE-2026-40399 | Windows TCP/IP Elevation of Privilege Vulnerability |
| CVE-2026-40407 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-40408 | Windows WAN ARP Driver Elevation of Privilege Vulnerability |
| CVE-2026-40410 | Windows SMB Client Elevation of Privilege Vulnerability |
| CVE-2026-40417 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability |
| CVE-2026-40418 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-40419 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-41086 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability |
| CVE-2026-41088 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-41095 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-41613 | Visual Studio Code Elevation of Privilege Vulnerability |
| CVE-2026-42823 | Azure Logic Apps Elevation of Privilege Vulnerability |
| CVE-2026-42825 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-42830 | Azure Monitor Agent Metrics Extension Elevation of Privilege Vulnerability |
| CVE-2026-42896 | Windows DWM Core Library Elevation of Privilege Vulnerability |
Remote Code Execution (31 CVEs)
| Critical severity | |
| CVE-2026-32161 | Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability |
| CVE-2026-33109 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability |
| CVE-2026-33844 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability |
| CVE-2026-35421 | Windows GDI Remote Code Execution Vulnerability |
| CVE-2026-40358 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40363 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40365 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40403 | Windows Graphics Component Remote Code Execution Vulnerability |
| CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability |
| CVE-2026-41096 | Windows DNS Client Remote Code Execution Vulnerability |
| CVE-2026-42831 | Office for Android Remote Code Execution Vulnerability |
| CVE-2026-42898 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-33110 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-33112 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-34329 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2026-34332 | Windows Kernel-Mode Driver Remote Code Execution Vulnerability |
| CVE-2026-35439 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40357 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40359 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40362 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40366 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40368 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40370 | SQL Server Remote Code Execution Vulnerability |
| CVE-2026-40380 | Windows Volume Manager Extension Driver Remote Code Execution Vulnerability |
| CVE-2026-40415 | Windows TCP/IP Remote Code Execution Vulnerability |
| CVE-2026-41094 | Microsoft Data Formulator Remote Code Execution Vulnerability |
| CVE-2026-41611 | Visual Studio Code Remote Code Execution Vulnerability |
| CVE-2026-42833 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability |
Information Disclosure (14 CVEs)
| Critical severity | |
| CVE-2026-26129 | M365 Copilot Information Disclosure Vulnerability |
| CVE-2026-26164 | M365 Copilot Information Disclosure Vulnerability |
| CVE-2026-33111 | Copilot Chat (Microsoft Edge) Information Disclosure Vulnerability |
| CVE-2026-33823 | Microsoft Team Events Portal Information Disclosure Vulnerability |
| CVE-2026-42826 | Azure DevOps Information Disclosure Vulnerability |
| Important severity | |
| CVE-2026-34336 | Windows DWM Core Library Information Disclosure Vulnerability |
| CVE-2026-35419 | Windows DWM Core Library Information Disclosure Vulnerability |
| CVE-2026-35423 | Windows 11 Telnet Client Information Disclosure Vulnerability |
| CVE-2026-35440 | Microsoft Word Information Disclosure Vulnerability |
| CVE-2026-40360 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-40374 | Microsoft Power Automate Desktop Information Disclosure Vulnerability |
| CVE-2026-40406 | Windows TCP/IP Information Disclosure Vulnerability |
| CVE-2026-40421 | Microsoft Word Information Disclosure Vulnerability |
| CVE-2026-41612 | Visual Studio Code Information Disclosure Vulnerability |
Spoofing (11 CVEs)
| Critical severity | |
| CVE-2026-32207 | Azure Machine Learning Notebook Spoofing Vulnerability |
| CVE-2026-34327 | Microsoft Partner Center Spoofing Vulnerability |
| CVE-2026-35428 | Azure Cloud Shell Spoofing Vulnerability |
| CVE-2026-40379 | Microsoft Enterprise Security Token Service (ESTS) Spoofing Vulnerability |
| Important severity | |
| CVE-2026-32185 | Microsoft Teams Spoofing Vulnerability |
| CVE-2026-33833 | Azure Machine Learning Notebook Spoofing Vulnerability |
| CVE-2026-41100 | Microsoft 365 Copilot for Android Spoofing Vulnerability |
| CVE-2026-41101 | Microsoft Word for Android Spoofing Vulnerability |
| CVE-2026-41102 | Microsoft PowerPoint for Android Spoofing Vulnerability |
| CVE-2026-41614 | M365 Copilot for Desktop Spoofing Vulnerability |
| CVE-2026-42832 | Microsoft Excel Spoofing Vulnerability |
Denial of Service (8 CVEs)
| Important severity | |
| CVE-2026-34339 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability |
| CVE-2026-34350 | Windows Storport Miniport Driver Denial of Service Vulnerability |
| CVE-2026-35424 | Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability |
| CVE-2026-40401 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40405 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40413 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40414 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-42899 | ASP.NET Core Denial of Service Vulnerability |
Security Feature Bypass (6 CVEs)
| Important severity | |
| CVE-2026-32209 | Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability |
| CVE-2026-33117 | Azure SDK for Java Security Feature Bypass Vulnerability |
| CVE-2026-35422 | Windows TCP/IP Driver Security Feature Bypass Vulnerability |
| CVE-2026-41097 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-41109 | GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability |
| CVE-2026-41610 | Visual Studio Code Security Feature Bypass Vulnerability |
Tampering (3 CVEs)
| Important severity | |
| CVE-2026-32175 | .NET Core Tampering Vulnerability |
| CVE-2026-40420 | Microsoft Office Click-To-Run Tampering Vulnerability |
| CVE-2026-42893 | Microsoft Outlook for iOS Tampering Vulnerability |
Appendix B: Exploitability and CVSS
This is a list of the 13 May CVEs judged by Microsoft to be more likely to be exploited in the wild within the first 30 days post-release. The list is arranged by CVE.
| Exploitation more likely within the next 30 days | |
| CVE-2026-33835 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-33837 | Windows TCP/IP Local Elevation of Privilege Vulnerability |
| CVE-2026-33840 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33841 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-35416 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-35417 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-35435 | Azure AI Foundry Elevation of Privilege Vulnerability |
| CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40369 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-40397 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-40398 | Windows Remote Desktop Services Elevation of Privilege Vulnerability |
| CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability |
These are the May CVEs with a Microsoft-assessed CVSS Base score of 8.0 or higher. They are arranged by score and further sorted by CVE. For more information on how CVSS works, please see our series on patch prioritization schema.
| CVSS Base | CVSS Temporal | CVE | Title |
| 10.0 | 8.7 | CVE-2026-42826 | Azure DevOps Information Disclosure Vulnerability |
| 9.9 | 8.6 | CVE-2026-33109 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability |
| 9.9 | 8.6 | CVE-2026-42823 | Azure Logic Apps Elevation of Privilege Vulnerability |
| 9.9 | 8.6 | CVE-2026-42898 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability |
| 9.8 | 8.5 | CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability |
| 9.8 | 8.5 | CVE-2026-41096 | Windows DNS Client Remote Code Execution Vulnerability |
| 9.6 | 8.3 | CVE-2026-33823 | Microsoft Team Events Portal Information Disclosure Vulnerability |
| 9.6 | 8.6 | CVE-2026-35428 | Azure Cloud Shell Spoofing Vulnerability |
| 9.3 | 8.1 | CVE-2026-40379 | Microsoft Enterprise Security Token Service (ESTS) Spoofing Vulnerability |
| 9.3 | 8.1 | CVE-2026-40402 | Windows Hyper-V Elevation of Privilege Vulnerability |
| 9.1 | 7.9 | CVE-2026-33117 | Azure SDK for Java Security Feature Bypass Vulnerability |
| 9.1 | 7.9 | CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability |
| 9.1 | 7.9 | CVE-2026-42833 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability |
| 9.0 | 7.8 | CVE-2026-33844 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-32207 | Azure Machine Learning Notebook Spoofing Vulnerability |
| 8.8 | 7.7 | CVE-2026-33110 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-33112 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-34329 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-35436 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-35439 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-40357 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-40365 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-40370 | SQL Server Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-40403 | Windows Graphics Component Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-40420 | Microsoft Office Click-To-Run Tampering Vulnerability |
| 8.8 | 7.7 | CVE-2026-41086 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-41094 | Microsoft Data Formulator Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-41109 | GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability |
| 8.8 | 7.7 | CVE-2026-41613 | Visual Studio Code Elevation of Privilege Vulnerability |
| 8.6 | 7.5 | CVE-2026-35435 | Azure AI Foundry Elevation of Privilege Vulnerability |
| 8.4 | 7.3 | CVE-2026-40358 | Microsoft Office Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-40363 | Microsoft Office Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-40366 | Microsoft Word Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability |
| 8.3 | 7.2 | CVE-2026-35438 | Windows Admin Center Elevation of Privilege Vulnerability |
| 8.2 | 7.1 | CVE-2026-33833 | Azure Machine Learning Notebook Spoofing Vulnerability |
| 8.2 | 7.1 | CVE-2026-34327 | Microsoft Partner Center Spoofing Vulnerability |
| 8.1 | 7.1 | CVE-2026-40415 | Windows TCP/IP Remote Code Execution Vulnerability |
| 8.1 | 7.1 | CVE-2026-41105 | Azure Monitor Action Group Notification System Elevation of Privilege Vulnerability |
| 8.0 | 7.0 | CVE-2026-34332 | Windows Kernel-Mode Driver Remote Code Execution Vulnerability |
| 8.0 | 7.0 | CVE-2026-40368 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Appendix C: Products Affected
This is a list of May’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple times, once for each product family. All CVE titles are accurate as made available by Microsoft. For further information on why certain products may appear in titles and not product families (or vice versa), please consult Microsoft.
Windows (68 CVEs)
| Critical severity | |
| CVE-2026-32161 | Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability |
| CVE-2026-35421 | Windows GDI Remote Code Execution Vulnerability |
| CVE-2026-40402 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2026-40403 | Windows Graphics Component Remote Code Execution Vulnerability |
| CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability |
| CVE-2026-41096 | Windows DNS Client Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-21530 | Windows Rich Text Edit Elevation of Privilege Vulnerability |
| CVE-2026-32170 | Windows Rich Text Edit Elevation of Privilege Vulnerability |
| CVE-2026-32209 | Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability |
| CVE-2026-33834 | Windows Event Logging Service Elevation of Privilege Vulnerability |
| CVE-2026-33835 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-33837 | Windows TCP/IP Local Elevation of Privilege Vulnerability |
| CVE-2026-33838 | Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2026-33839 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33840 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33841 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-34329 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2026-34330 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34331 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34332 | Windows Kernel-Mode Driver Remote Code Execution Vulnerability |
| CVE-2026-34333 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34334 | Windows TCP/IP Elevation of Privilege Vulnerability |
| CVE-2026-34336 | Windows DWM Core Library Information Disclosure Vulnerability |
| CVE-2026-34337 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-34338 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-34339 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability |
| CVE-2026-34340 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-34341 | Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability |
| CVE-2026-34342 | Windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2026-34343 | Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability |
| CVE-2026-34344 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-34345 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-34347 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-34350 | Windows Storport Miniport Driver Denial of Service Vulnerability |
| CVE-2026-34351 | Windows TCP/IP Elevation of Privilege Vulnerability |
| CVE-2026-35415 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability |
| CVE-2026-35416 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-35417 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-35418 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-35419 | Windows DWM Core Library Information Disclosure Vulnerability |
| CVE-2026-35420 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-35422 | Windows TCP/IP Driver Security Feature Bypass Vulnerability |
| CVE-2026-35423 | Windows 11 Telnet Client Information Disclosure Vulnerability |
| CVE-2026-35424 | Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability |
| CVE-2026-40369 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-40377 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability |
| CVE-2026-40380 | Windows Volume Manager Extension Driver Remote Code Execution Vulnerability |
| CVE-2026-40382 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-40397 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-40398 | Windows Remote Desktop Services Elevation of Privilege Vulnerability |
| CVE-2026-40399 | Windows TCP/IP Elevation of Privilege Vulnerability |
| CVE-2026-40401 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40405 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40406 | Windows TCP/IP Information Disclosure Vulnerability |
| CVE-2026-40407 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-40408 | Windows WAN ARP Driver Elevation of Privilege Vulnerability |
| CVE-2026-40410 | Windows SMB Client Elevation of Privilege Vulnerability |
| CVE-2026-40413 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40414 | Windows TCP/IP Denial of Service Vulnerability |
| CVE-2026-40415 | Windows TCP/IP Remote Code Execution Vulnerability |
| CVE-2026-41088 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-41095 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-41097 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-42825 | Windows Telephony Service Elevation of Privilege Vulnerability |
| CVE-2026-42896 | Windows DWM Core Library Elevation of Privilege Vulnerability |
Office (16 CVEs)
| Critical severity | |
| CVE-2026-40358 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40363 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-42831 | Office for Android Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-35436 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-35440 | Microsoft Word Information Disclosure Vulnerability |
| CVE-2026-40359 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40360 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-40362 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40366 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40418 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-40419 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-40420 | Microsoft Office Click-To-Run Tampering Vulnerability |
| CVE-2026-40421 | Microsoft Word Information Disclosure Vulnerability |
365 (15 CVEs)
| Critical severity | |
| CVE-2026-40358 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40363 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-35436 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-35440 | Microsoft Word Information Disclosure Vulnerability |
| CVE-2026-40359 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40360 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-40362 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40366 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40418 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-40419 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability |
| CVE-2026-40420 | Microsoft Office Click-To-Run Tampering Vulnerability |
| CVE-2026-40421 | Microsoft Word Information Disclosure Vulnerability |
Azure (15 CVEs)
| Critical severity | |
| CVE-2026-32207 | Azure Machine Learning Notebook Spoofing Vulnerability |
| CVE-2026-33109 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability |
| CVE-2026-33844 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability |
| CVE-2026-35428 | Azure Cloud Shell Spoofing Vulnerability |
| CVE-2026-35435 | Azure AI Foundry Elevation of Privilege Vulnerability |
| CVE-2026-40379 | Microsoft Enterprise Security Token Service (ESTS) Spoofing Vulnerability |
| CVE-2026-41105 | Azure Monitor Action Group Notification System Elevation of Privilege Vulnerability |
| CVE-2026-42826 | Azure DevOps Information Disclosure Vulnerability |
| Important severity | |
| CVE-2026-32204 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2026-33117 | Azure SDK for Java Security Feature Bypass Vulnerability |
| CVE-2026-33833 | Azure Machine Learning Notebook Spoofing Vulnerability |
| CVE-2026-40381 | Azure Connected Machine Agent Elevation of Privilege Vulnerability |
| CVE-2026-41086 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability |
| CVE-2026-42823 | Azure Logic Apps Elevation of Privilege Vulnerability |
| CVE-2026-42830 | Azure Monitor Agent Metrics Extension Elevation of Privilege Vulnerability |
SharePoint (7 CVEs)
| Critical severity | |
| CVE-2026-40365 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-33110 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-33112 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-35439 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40357 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2026-40368 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Visual Studio (7 CVEs)
| Important severity | |
| CVE-2026-32175 | .NET Core Tampering Vulnerability |
| CVE-2026-32177 | .NET Elevation of Privilege Vulnerability |
| CVE-2026-41109 | GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability |
| CVE-2026-41610 | Visual Studio Code Security Feature Bypass Vulnerability |
| CVE-2026-41611 | Visual Studio Code Remote Code Execution Vulnerability |
| CVE-2026-41612 | Visual Studio Code Information Disclosure Vulnerability |
| CVE-2026-41613 | Visual Studio Code Elevation of Privilege Vulnerability |
Word (7 CVEs)
| Critical severity | |
| CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-35440 | Microsoft Word Information Disclosure Vulnerability |
| CVE-2026-40366 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-40421 | Microsoft Word Information Disclosure Vulnerability |
| CVE-2026-41101 | Microsoft Word for Android Spoofing Vulnerability |
Copilot (5 CVEs)
| Critical severity | |
| CVE-2026-26129 | M365 Copilot Information Disclosure Vulnerability |
| CVE-2026-26164 | M365 Copilot Information Disclosure Vulnerability |
| CVE-2026-33111 | Copilot Chat (Microsoft Edge) Information Disclosure Vulnerability |
| Important severity | |
| CVE-2026-41100 | Microsoft 365 Copilot for Android Spoofing Vulnerability |
| CVE-2026-41614 | M365 Copilot for Desktop Spoofing Vulnerability |
.NET (4 CVEs)
| Important severity | |
| CVE-2026-32175 | .NET Core Tampering Vulnerability |
| CVE-2026-32177 | .NET Elevation of Privilege Vulnerability |
| CVE-2026-35433 | .NET Elevation of Privilege Vulnerability |
| CVE-2026-42899 | ASP.NET Core Denial of Service Vulnerability |
Dynamics 365 (4 CVEs)
| Critical severity | |
| CVE-2026-33821 | Microsoft Dynamics 365 Customer Insights Elevation of Privilege Vulnerability |
| CVE-2026-42898 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-40417 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability |
| CVE-2026-42833 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability |
Excel (4 CVEs)
| Important severity | |
| CVE-2026-40359 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-40360 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-40362 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-42832 | Microsoft Excel Spoofing Vulnerability |
Teams (2 CVEs)
| Critical severity | |
| CVE-2026-33823 | Microsoft Team Events Portal Information Disclosure Vulnerability |
| Important severity | |
| CVE-2026-32185 | Microsoft Teams Spoofing Vulnerability |
Confluence / Jira (1 CVE)
| Critical severity | |
| CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability |
Data Formulator (1 CVE)
| Important severity | |
| CVE-2026-41094 | Microsoft Data Formulator Remote Code Execution Vulnerability |
Outlook (1 CVE)
| Important severity | |
| CVE-2026-42893 | Microsoft Outlook for iOS Tampering Vulnerability |
Partner Center (1 CVE)
| Critical severity | |
| CVE-2026-34327 | Microsoft Partner Center Spoofing Vulnerability |
Power Automate (1 CVE)
| Important severity | |
| CVE-2026-40374 | Microsoft Power Automate Desktop Information Disclosure Vulnerability |
PowerPoint(1 CVE)
| Important severity | |
| CVE-2026-41102 | Microsoft PowerPoint for Android Spoofing Vulnerability |
SQL (1 CVE)
| Important severity | |
| CVE-2026-40370 | SQL Server Remote Code Execution Vulnerability |
Windows Admin Center (1 CVE)
| Important severity | |
| CVE-2026-35438 | Windows Admin Center Elevation of Privilege Vulnerability |
Appendix D: Advisories and Other Products
There are 131 Edge-related advisories listed in May’s release, all but five from Chrome. Because the CVEs from Microsoft were (like the Chrome CVEs) patched before Patch Tuesday, and because this post is already shockingly long, we have massed all of them together in the very long table below.
| CVE-2026-7896 | Chromium: CVE-2026-7896 Integer overflow in Blink |
| CVE-2026-7897 | Chromium: CVE-2026-7897 Use after free in Mobile |
| CVE-2026-7898 | Chromium: CVE-2026-7898 Use after free in Chromoting |
| CVE-2026-7899 | Chromium: CVE-2026-7899 Out of bounds read and write in V8 |
| CVE-2026-7900 | Chromium: CVE-2026-7900 Heap buffer overflow in ANGLE |
| CVE-2026-7901 | Chromium: CVE-2026-7901 Use after free in ANGLE |
| CVE-2026-7902 | Chromium: CVE-2026-7902 Out of bounds memory access in V8 |
| CVE-2026-7903 | Chromium: CVE-2026-7903 Integer overflow in ANGLE |
| CVE-2026-7904 | Chromium: CVE-2026-7904 Out of bounds read in Fonts |
| CVE-2026-7905 | Chromium: CVE-2026-7905 Insufficient validation of untrusted input in Media |
| CVE-2026-7906 | Chromium: CVE-2026-7906 Use after free in SVG |
| CVE-2026-7907 | Chromium: CVE-2026-7907 Use after free in DOM |
| CVE-2026-7908 | Chromium: CVE-2026-7908 Use after free in Fullscreen |
| CVE-2026-7909 | Chromium: CVE-2026-7909 Inappropriate implementation in ServiceWorker |
| CVE-2026-7910 | Chromium: CVE-2026-7910 Use after free in Views |
| CVE-2026-7911 | Chromium: CVE-2026-7911 Use after free in Aura |
| CVE-2026-7912 | Chromium: CVE-2026-7912 Integer overflow in GPU |
| CVE-2026-7913 | Chromium: CVE-2026-7913 Insufficient policy enforcement in DevTools |
| CVE-2026-7914 | Chromium: CVE-2026-7914 Type Confusion in Accessibility |
| CVE-2026-7915 | Chromium: CVE-2026-7915 Insufficient data validation in DevTools |
| CVE-2026-7916 | Chromium: CVE-2026-7916 Insufficient data validation in InterestGroups |
| CVE-2026-7917 | Chromium: CVE-2026-7917 Use after free in Fullscreen |
| CVE-2026-7918 | Chromium: CVE-2026-7918 Use after free in GPU |
| CVE-2026-7919 | Chromium: CVE-2026-7919 Use after free in Aura |
| CVE-2026-7920 | Chromium: CVE-2026-7920 Use after free in Skia |
| CVE-2026-7921 | Chromium: CVE-2026-7921 Use after free in Passwords |
| CVE-2026-7922 | Chromium: CVE-2026-7922 Use after free in ServiceWorker |
| CVE-2026-7923 | Chromium: CVE-2026-7923 Out of bounds write in Skia |
| CVE-2026-7924 | Chromium: CVE-2026-7924 Uninitialized Use in Dawn |
| CVE-2026-7925 | Chromium: CVE-2026-7925 Use after free in Chromoting |
| CVE-2026-7926 | Chromium: CVE-2026-7926 Use after free in PresentationAPI |
| CVE-2026-7927 | Chromium: CVE-2026-7927 Type Confusion in Runtime |
| CVE-2026-7928 | Chromium: CVE-2026-7928 Use after free in WebRTC |
| CVE-2026-7929 | Chromium: CVE-2026-7929 Use after free in MediaRecording |
| CVE-2026-7930 | Chromium: CVE-2026-7930 Insufficient validation of untrusted input in Cookies |
| CVE-2026-7931 | Chromium: CVE-2026-7931 Insufficient validation of untrusted input in iOS |
| CVE-2026-7932 | Chromium: CVE-2026-7932 Insufficient policy enforcement in Downloads |
| CVE-2026-7933 | Chromium: CVE-2026-7933 Out of bounds read in WebCodecs |
| CVE-2026-7934 | Chromium: CVE-2026-7934 Insufficient validation of untrusted input in Popup Blocker |
| CVE-2026-7935 | Chromium: CVE-2026-7935 Inappropriate implementation in Speech |
| CVE-2026-7936 | Chromium: CVE-2026-7936 Object lifecycle issue in V8 |
| CVE-2026-7937 | Chromium: CVE-2026-7937 Insufficient policy enforcement in DevTools |
| CVE-2026-7938 | Chromium: CVE-2026-7938 Use after free in CSS |
| CVE-2026-7939 | Chromium: CVE-2026-7939 Inappropriate implementation in SanitizerAPI |
| CVE-2026-7940 | Chromium: CVE-2026-7940 Use after free in V8 |
| CVE-2026-7941 | Chromium: CVE-2026-7941 Insufficient validation of untrusted input in Mobile |
| CVE-2026-7942 | Chromium: CVE-2026-7942 Integer overflow in ANGLE |
| CVE-2026-7943 | Chromium: CVE-2026-7943 Insufficient validation of untrusted input in ANGLE |
| CVE-2026-7944 | Chromium: CVE-2026-7944 Insufficient validation of untrusted input in Persistent Cache |
| CVE-2026-7945 | Chromium: CVE-2026-7945 Insufficient validation of untrusted input in COOP |
| CVE-2026-7946 | Chromium: CVE-2026-7946 Insufficient policy enforcement in WebUI |
| CVE-2026-7947 | Chromium: CVE-2026-7947 Insufficient validation of untrusted input in Network |
| CVE-2026-7948 | Chromium: CVE-2026-7948 Race in Chromoting |
| CVE-2026-7949 | Chromium: CVE-2026-7949 Out of bounds read in Skia |
| CVE-2026-7950 | Chromium: CVE-2026-7950 Out of bounds read and write in GFX |
| CVE-2026-7951 | Chromium: CVE-2026-7951 Out of bounds write in WebRTC |
| CVE-2026-7952 | Chromium: CVE-2026-7952 Insufficient policy enforcement in Extensions |
| CVE-2026-7953 | Chromium: CVE-2026-7953 Insufficient validation of untrusted input in Omnibox |
| CVE-2026-7954 | Chromium: CVE-2026-7954 Race in Shared Storage |
| CVE-2026-7955 | Chromium: CVE-2026-7955 Uninitialized Use in GPU |
| CVE-2026-7956 | Chromium: CVE-2026-7956 Use after free in Navigation |
| CVE-2026-7957 | Chromium: CVE-2026-7957 Out of bounds write in Media |
| CVE-2026-7958 | Chromium: CVE-2026-7958 Inappropriate implementation in ServiceWorker |
| CVE-2026-7959 | Chromium: CVE-2026-7959 Inappropriate implementation in Navigation |
| CVE-2026-7960 | Chromium: CVE-2026-7960 Race in Speech |
| CVE-2026-7961 | Chromium: CVE-2026-7961 Insufficient validation of untrusted input in Permissions |
| CVE-2026-7962 | Chromium: CVE-2026-7962 Insufficient policy enforcement in DirectSockets |
| CVE-2026-7963 | Chromium: CVE-2026-7963 Inappropriate implementation in ServiceWorker |
| CVE-2026-7964 | Chromium: CVE-2026-7964 Insufficient validation of untrusted input in FileSystem |
| CVE-2026-7965 | Chromium: CVE-2026-7965 Insufficient validation of untrusted input in DevTools |
| CVE-2026-7966 | Chromium: CVE-2026-7966 Insufficient validation of untrusted input in SiteIsolation |
| CVE-2026-7967 | Chromium: CVE-2026-7967 Insufficient validation of untrusted input in Navigation |
| CVE-2026-7968 | Chromium: CVE-2026-7968 Insufficient validation of untrusted input in CORS |
| CVE-2026-7969 | Chromium: CVE-2026-7969 Integer overflow in Network |
| CVE-2026-7970 | Chromium: CVE-2026-7970 Use after free in TopChrome |
| CVE-2026-7971 | Chromium: CVE-2026-7971 Inappropriate implementation in ORB |
| CVE-2026-7972 | Chromium: CVE-2026-7972 Uninitialized Use in GPU |
| CVE-2026-7973 | Chromium: CVE-2026-7973 Integer overflow in Dawn |
| CVE-2026-7974 | Chromium: CVE-2026-7974 Use after free in Blink |
| CVE-2026-7975 | Chromium: CVE-2026-7975 Use after free in DevTools |
| CVE-2026-7976 | Chromium: CVE-2026-7976 Use after free in Views |
| CVE-2026-7977 | Chromium: CVE-2026-7977 Inappropriate implementation in Canvas |
| CVE-2026-7978 | Chromium: CVE-2026-7978 Inappropriate implementation in Companion |
| CVE-2026-7979 | Chromium: CVE-2026-7979 Inappropriate implementation in Media |
| CVE-2026-7980 | Chromium: CVE-2026-7980 Use after free in WebAudio |
| CVE-2026-7981 | Chromium: CVE-2026-7981 Out of bounds read in Codecs |
| CVE-2026-7982 | Chromium: CVE-2026-7982 Uninitialized Use in WebCodecs |
| CVE-2026-7983 | Chromium: CVE-2026-7983 Out of bounds read in Dawn |
| CVE-2026-7984 | Chromium: CVE-2026-7984 Use after free in ReadingMode |
| CVE-2026-7985 | Chromium: CVE-2026-7985 Use after free in GPU |
| CVE-2026-7986 | Chromium: CVE-2026-7986 Insufficient policy enforcement in Autofill |
| CVE-2026-7987 | Chromium: CVE-2026-7987 Use after free in WebRTC |
| CVE-2026-7988 | Chromium: CVE-2026-7988 Type Confusion in WebRTC |
| CVE-2026-7989 | Chromium: CVE-2026-7989 Insufficient data validation in DataTransfer |
| CVE-2026-7990 | Chromium: CVE-2026-7990 Insufficient validation of untrusted input in Updater |
| CVE-2026-7991 | Chromium: CVE-2026-7991 Use after free in UI |
| CVE-2026-7992 | Chromium: CVE-2026-7992 Insufficient validation of untrusted input in UI |
| CVE-2026-7993 | Chromium: CVE-2026-7993 Insufficient validation of untrusted input in Payments |
| CVE-2026-7994 | Chromium: CVE-2026-7994 Inappropriate implementation in Chromoting |
| CVE-2026-7995 | Chromium: CVE-2026-7995 Out of bounds read in AdFilter |
| CVE-2026-7996 | Chromium: CVE-2026-7996 Insufficient validation of untrusted input in SSL |
| CVE-2026-7997 | Chromium: CVE-2026-7997 Insufficient validation of untrusted input in Updater |
| CVE-2026-7998 | Chromium: CVE-2026-7998 Insufficient validation of untrusted input in Dialog |
| CVE-2026-7999 | Chromium: CVE-2026-7999 Inappropriate implementation in V8 |
| CVE-2026-8000 | Chromium: CVE-2026-8000 Insufficient validation of untrusted input in ChromeDriver |
| CVE-2026-8001 | Chromium: CVE-2026-8001 Use after free in Printing |
| CVE-2026-8002 | Chromium: CVE-2026-8002 Use after free in Audio |
| CVE-2026-8003 | Chromium: CVE-2026-8003 Insufficient validation of untrusted input in TabGroups |
| CVE-2026-8004 | Chromium: CVE-2026-8004 Insufficient policy enforcement in DevTools |
| CVE-2026-8005 | Chromium: CVE-2026-8005 Insufficient validation of untrusted input in Cast |
| CVE-2026-8006 | Chromium: CVE-2026-8006 Insufficient policy enforcement in DevTools |
| CVE-2026-8007 | Chromium: CVE-2026-8007 Insufficient validation of untrusted input in Cast |
| CVE-2026-8008 | Chromium: CVE-2026-8008 Inappropriate implementation in DevTools |
| CVE-2026-8009 | Chromium: CVE-2026-8009 Inappropriate implementation in Cast |
| CVE-2026-8010 | Chromium: CVE-2026-8010 Insufficient validation of untrusted input in SiteIsolation |
| CVE-2026-8011 | Chromium: CVE-2026-8011 Insufficient policy enforcement in Search |
| CVE-2026-8012 | Chromium: CVE-2026-8012 Inappropriate implementation in MHTML |
| CVE-2026-8013 | Chromium: CVE-2026-8013 Insufficient validation of untrusted input in FedCM |
| CVE-2026-8014 | Chromium: CVE-2026-8014 Inappropriate implementation in Preload |
| CVE-2026-8015 | Chromium: CVE-2026-8015 Inappropriate implementation in Media |
| CVE-2026-8016 | Chromium: CVE-2026-8016 Use after free in WebRTC |
| CVE-2026-8017 | Chromium: CVE-2026-8017 Side-channel information leakage in Media |
| CVE-2026-8018 | Chromium: CVE-2026-8018 Insufficient policy enforcement in DevTools |
| CVE-2026-8019 | Chromium: CVE-2026-8019 Insufficient policy enforcement in WebApp |
| CVE-2026-8020 | Chromium: CVE-2026-8020 Uninitialized Use in GPU |
| CVE-2026-8021 | Chromium: CVE-2026-8021 Script injection in UI |
| CVE-2026-8022 | Chromium: CVE-2026-8022 Inappropriate implementation in MHTML |
| CVE-2026-35429 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability |
| CVE-2026-40416 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability |
| CVE-2026-41107 | Microsoft Edge (Chromium-based) Information Disclosure Vulnerability |
| CVE-2026-42838 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability |
| CVE-2026-42891 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability |
Meanwhile, there are 13 updates from Adobe, all affecting Adobe Commerce - 2.4.9, 2.4.8-p5, 2.4.7-p10, 2.4.6-p15, 2.4.5-p17, 2.4.4-p18. These are collectively addresseḍ as APSB26-49.
| CVE-2026-34645 | Incorrect Authorization (CWE-863) |
| CVE-2026-34646 | Incorrect Authorization (CWE-863) |
| CVE-2026-34647 | Server-Side Request Forgery (SSRF) (CWE-918) |
| CVE-2026-34648 | Uncontrolled Resource Consumption (CWE-400) |
| CVE-2026-34649 | Uncontrolled Resource Consumption (CWE-400) |
| CVE-2026-34650 | Uncontrolled Resource Consumption (CWE-400) |
| CVE-2026-34651 | Uncontrolled Resource Consumption (CWE-400) |
| CVE-2026-34652 | Dependency on Vulnerable Third-Party Component (CWE-1395) |
| CVE-2026-34653 | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') (CWE-22) |
| CVE-2026-34654 | Dependency on Vulnerable Third-Party Component (CWE-1395) |
| CVE-2026-34655 | Cross-site Scripting (Stored XSS) (CWE-79) |
| CVE-2026-34656 | Improper Authorization (CWE-285) |
| CVE-2026-34658 | Cross-site Scripting (Stored XSS) (CWE-79) |
Microsoft also issued the usual servicing stack updates this month (ADV990000).
Finally, there is one Important-severity CVE from AMD (CVE-2025-54518, CPU OP Cache Corruption) in this month’s set; we have covered it elsewhere in this post, including in the table below. Microsoft is releasing advisory information on this issue to state that the latest builds of windows protect against this cache-corruption vulnerability.
Appendix E: Affected Windows Server versions
This is a table of 66 CVEs in the May release affecting Windows Server versions 2012 through 2025. The table differentiates among major versions of the platform but doesn’t go into deeper detail (eg., Server Core). An “x” indicates that the CVE does not apply to that version. We include the Important-severity, Windows-touching advisory from AMD, since the Server versions they affect are known; those are indicated in this chart in blue.
Administrators are encouraged to use this appendix as a starting point to ascertain their specific exposure, as each reader’s situation, especially as it concerns products out of mainstream support, will vary. For specific Knowledge Base numbers, please consult Microsoft.
| CVE | S-12 | 12r2 | S-16 | S-19 | S-22 | 23h2 | S-25 |
| CVE-2025-54518 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-21530 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-32161 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-32170 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-32209 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-33834 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-33835 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-33837 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-33838 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-33839 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-33840 | × | × | × | × | × | × | ■ |
| CVE-2026-33841 | × | × | × | × | ■ | ■ | ■ |
| CVE-2026-34329 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34330 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34331 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34332 | × | × | × | × | × | × | ■ |
| CVE-2026-34333 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34334 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34336 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34337 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-34338 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34339 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34340 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-34341 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34342 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34343 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34344 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34345 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34347 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-34350 | × | × | × | × | × | × | ■ |
| CVE-2026-34351 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35415 | × | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35416 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35417 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-35418 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-35419 | × | × | × | × | × | × | ■ |
| CVE-2026-35420 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35421 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35422 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35423 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-35424 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40369 | × | × | × | × | × | × | ■ |
| CVE-2026-40377 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40380 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40382 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40397 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40398 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40399 | × | × | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40401 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40402 | × | × | × | × | ■ | × | × |
| CVE-2026-40403 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40405 | × | × | × | × | × | × | ■ |
| CVE-2026-40406 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40407 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40408 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40410 | × | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40413 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40414 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-40415 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-41088 | × | × | × | × | ■ | ■ | ■ |
| CVE-2026-41089 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-41095 | × | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-41096 | × | × | × | × | × | ■ | ■ |
| CVE-2026-41097 | × | × | × | ■ | ■ | ■ | ■ |
| CVE-2026-42825 | ■ | ■ | ■ | ■ | ■ | ■ | ■ |
| CVE-2026-42896 | × | × | × | × | × | × | ■ |
Appendix F: Common Weakness Enumeration
As mentioned above, Microsoft now states which CWEs affect the CVEs they address. This month, we looked at which CWEs were most heavily represented in the dataset and compared them to last month’s inaugural numbers. The May dataset of 132 CVEs gave us 152 CWEs overall; 17 CVEs had two CVEs, and 3 had three CWEs. There were 49 unique CWEs, slightly more than last month’s 42. Once again CWE-416, Use After Free, leads the pack, though it accounts for just 18.42 percent of vulnerabilities rather than the commanding 28.57 percent in April’s haul. With just two months’ worth of data it’s too early to identify significant patterns yet, but we once again find ourselves looking at CWE-835 -- Loop with Unreachable Exit Condition ('Infinite Loop') and asking why the number for that couldn’t be either zero (0) or a sideways eight (∞).
| CWE | Count | CWE Name |
| 416 | 28 | Use After Free |
| 122 | 18 | Heap-based Buffer Overflow |
| 284 | 13 | Improper Access Control |
| 362 | 8 | Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') |
| 476 | 6 | NULL Pointer Dereference |
| 502 | 5 | Deserialization of Untrusted Data |
| 190 | 5 | Integer Overflow or Wraparound |
| 415 | 4 | Double Free |
| 200 | 4 | Exposure of Sensitive Information to an Unauthorized Actor |
| 125 | 4 | Out-of-bounds Read |
| 77 | 4 | Improper Neutralization of Special Elements used in a Command ('Command Injection') |
| 73 | 4 | External Control of File Name or Path |
| 843 | 3 | Access of Resource Using Incompatible Type ('Type Confusion') |
| 74 | 3 | Improper Neutralization of Special Elements in Output Used by a Downstream Component ('Injection') |
| 20 | 3 | Improper Input Validation |
| 1220 | 2 | Insufficient Granularity of Access Control |
| 822 | 2 | Untrusted Pointer Dereference |
| 552 | 2 | Files or Directories Accessible to External Parties |
| 121 | 2 | Stack-based Buffer Overflow |
| 94 | 2 | Improper Control of Generation of Code ('Code Injection') |
| 79 | 2 | Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') |
| 1390 | 1 | Weak Authentication |
| 1329 | 1 | Reliance on Component That is Not Updateable |
| 918 | 1 | Server-Side Request Forgery (SSRF) |
| 908 | 1 | Use of Uninitialized Resource |
| 862 | 1 | Missing Authorization |
| 835 | 1 | Loop with Unreachable Exit Condition ('Infinite Loop') |
| 610 | 1 | Externally Controlled Reference to a Resource in Another Sphere |
| 426 | 1 | Untrusted Search Path |
| 401 | 1 | Missing Release of Memory after Effective Lifetime |
| 384 | 1 | Session Fixation |
| 367 | 1 | Time-of-check Time-of-use (TOCTOU) Race Condition |
| 347 | 1 | Improper Verification of Cryptographic Signature |
| 303 | 1 | Incorrect Implementation of Authentication Algorithm |
| 288 | 1 | Authentication Bypass Using an Alternate Path or Channel |
| 287 | 1 | Improper Authentication |
| 285 | 1 | Improper Authorization |
| 269 | 1 | Improper Privilege Management |
| 250 | 1 | Execution with Unnecessary Privileges |
| 197 | 1 | Numeric Truncation Error |
| 191 | 1 | Integer Underflow (Wrap or Wraparound) |
| 138 | 1 | Improper Neutralization of Special Elements |
| 126 | 1 | Buffer Over-read |
| 80 | 1 | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) |
| 78 | 1 | Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') |
| 59 | 1 | Improper Link Resolution Before File Access ('Link Following') |
| 36 | 1 | Absolute Path Traversal |
| 23 | 1 | Relative Path Traversal |
| 22 | 1 | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') |
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


