
Tap Into the Intelligence That Powers Sophos
SophosLabs Intelix was developed by SophosLabs, a critically acclaimed global Tier 1 threat research lab. It is used in Sophos' industry-leading cybersecurity solutions and lets you command the power of SophosLabs' threat research through a suite of simple, rapid-response RESTful APIs.

Powered by Data Science
Take advantage of industry-leading data science research into predictive analysis and detection through deep learning artificial neural networks and advanced learning and modeling techniques.

More Than Just Answers
Rich intelligence reports provide you with actionable insights into the nature and capabilities of a threat so you can answer the hardest questions about it.

Data Quality and Breadth
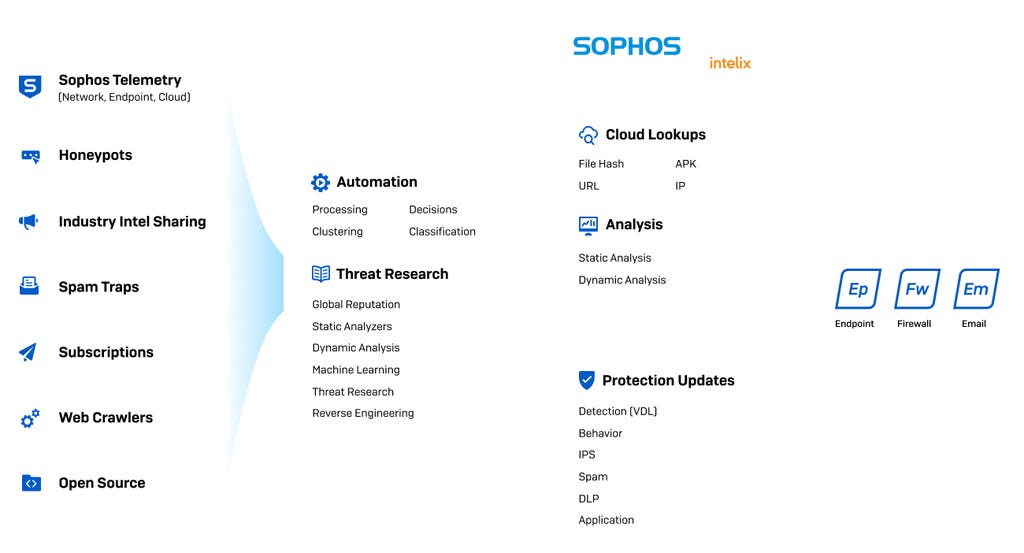
Access curated, aggregated, and consolidated threat intelligence sourced from disparate and complementary data sources with global intelligence from Sophos-protected networks, endpoints, and other sources.
SophosLabs Systems
Three Easy to Use APIs
Cloud Threat Lookups
Take advantage of industry-leading data science research into predictive analysis and detection through deep learning artificial neural networks and advanced learning and modelling techniques.Static File Analysis
Harness the power of multiple machine learning models, global reputation, deep file scanning, and more without needing to execute the file in real time.Dynamic File Analysis
Detonate malware in real-time in a sandbox utilizing the latest analysis techniques for unmatched visibility into malicious files to reveal the true nature and capabilities of a potential threat.
Don’t Compromise Security for Performance
SophosLabs Intelix makes it easy to rapidly identify and analyze threats
With our progressive suite of intelligence APIs, you can quickly identify known threats via Cloud Threat Lookups before moving on to file uploads for detailed analysis with Static and Dynamic File Analysis.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)

