When organizations select a cybersecurity vendor, they’re placing critical operational resilience — people, data, and revenue — into that supplier’s hands.
Yet despite this reliance, most organizations lack confidence in the vendors they depend on to keep them secure, according to new Sophos research.
To understand the reality of cybersecurity trust, Sophos commissioned an independent, vendor‑agnostic global survey of 5,000 IT and security decision‑makers across 17 countries. Conducted by Vanson Bourne, a specialist research firm, the survey provides a statistically significant, real‑world picture of how trust is built, and lost, between cybersecurity buyers and vendors.
Key findings from this research include:
- Trust is lacking: Only 5% of IT leaders say that both they and their organization have full trust in their cybersecurity vendors.
- Verified evidence is a primary driver of trust: IT teams and senior leadership agree that verifiable artifacts of cybersecurity maturity are the most significant indicator of trustworthiness.
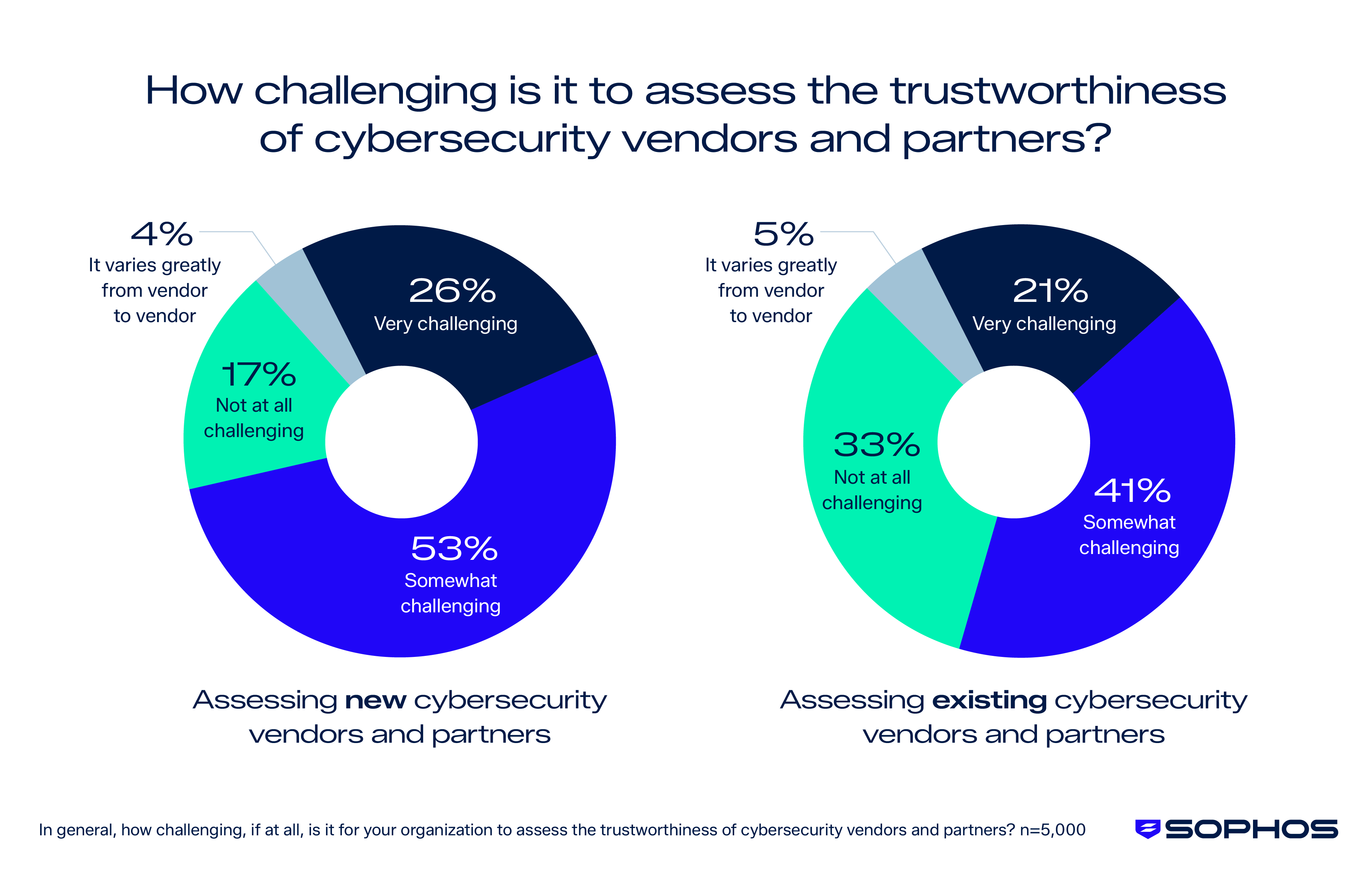
- Assessing vendor trustworthiness remains challenging: 79% of organizations find it challenging to assess the trustworthiness of new cybersecurity providers, while 62% find it challenging for their existing vendors.
- Respondents cited several factors that reduced confidence in vendors, chief among them being because information the vendor provided wasn’t factual or detailed enough.
- This lack of trust has consequences: 51% of respondents say that lack of trust leads to anxiety that the organization is more likely to experience a significant cyber incident.
- Practitioners and leadership don’t often agree: 78% of respondents say that their IT team and senior leadership team/ board differ in opinion on the trustworthiness of their organization’s cybersecurity vendors.
- Nearly one-third of companies who responded to Sophos’ survey say this disagreement happens “often.”
Want to keep these findings handy? Grab the report here.
Reported trust levels are low
Only 5% of IT leaders say that both they and their organization have full trust in their cybersecurity vendors.
When you’re looking to your cybersecurity vendor to keep your network secure and operations up and running, trust is key. Cybersecurity providers are the ones defending your business 24/7, even on nights and weekends, and when IT team members are on vacation. For small business owners, they may not even have dedicated IT staff, and their cybersecurity products or services can act like an employee of their own.
Before organizations can decide who to trust, they face an even more fundamental challenge: Simply evaluating a vendor’s trustworthiness in the first place.
According to the survey, 79% of respondents say it’s challenging to assess the trustworthiness of new cybersecurity vendors or partners, highlighting a widespread struggle to compare products, validate claims, and understand whether a prospective provider can truly safeguard the business. 62% also struggle to evaluate the trustworthiness of the vendors they’re already working with — a signal that trust gaps don’t disappear once a contract is signed.
Respondents pointed to several barriers to trust — most rooted in transparency. Many struggle to interpret vendor claims, assess technical details, or find the information they need to make confident decisions.
Nearly half (47%) say the information vendors provide isn’t factual or detailed enough, and 45% find that information hard to interpret or understand. A further 43% admit they lack the skills or knowledge to assess vendors effectively, 41% encounter conflicting information, and 38% struggle simply to find the information they need.
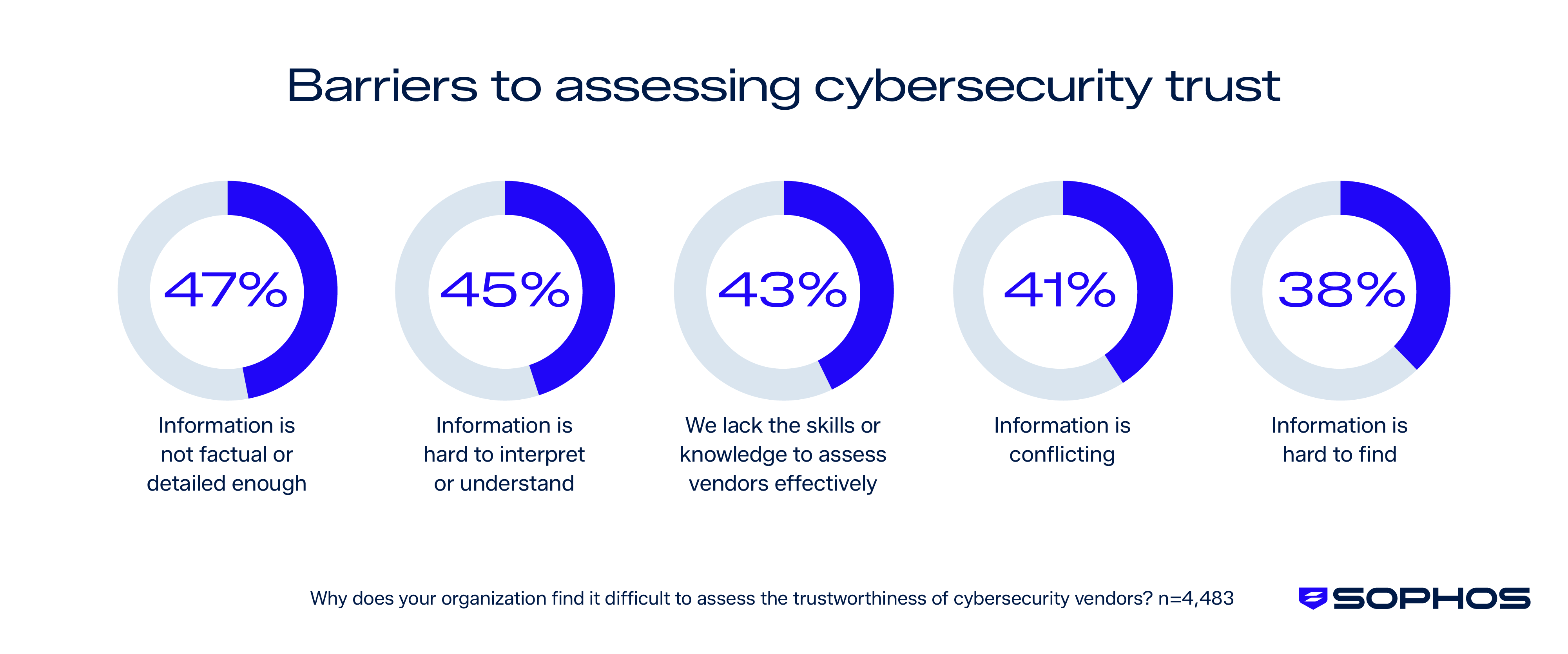
The biggest area of difference between small businesses (sub-250 employees) and enterprises (1,000+ employees) is that SMBs are much more likely to lack the skills or knowledge needed to assess vendor trustworthiness effectively — SMBs chose that as an issue 8% more than those respondents at enterprises.
Reported impacts of limited trust
This research quantifies the impact that a lack of trust between a security vendor and their customers is a significant issue in multiple ways. When asked about the impact of not having full trust in their cybersecurity vendors, respondents highlighted a mix of emotional and operational consequences:
- 51% report increased concern that their organization may experience a significant cyber incident.
- 45% say it makes them more likely to switch vendors — an expensive and disruptive process for most organizations.
- 42% see increased oversight requirements.
- 41% report reduced peace of mind regarding their cybersecurity posture.
- 38% report concern that they or their organization may have made an incorrect vendor selection.
These reported impacts add to the operational demands already placed on IT and cybersecurity teams.
Divergent assessments between IT and leadership
Another critical challenge is misalignment between the people using cybersecurity tools day‑to‑day and those signing off on the contracts. 78% of respondents say their IT team and senior leadership team or board differ in opinion on the trustworthiness of their cybersecurity vendors, and nearly a third say those disagreements happen often.
Respondents indicated that senior leadership remains highly involved in purchasing decisions. Only 1% of organizations reported that senior leadership plays no role in cybersecurity purchasing decisions.
Ways that cybersecurity companies can better cultivate trust
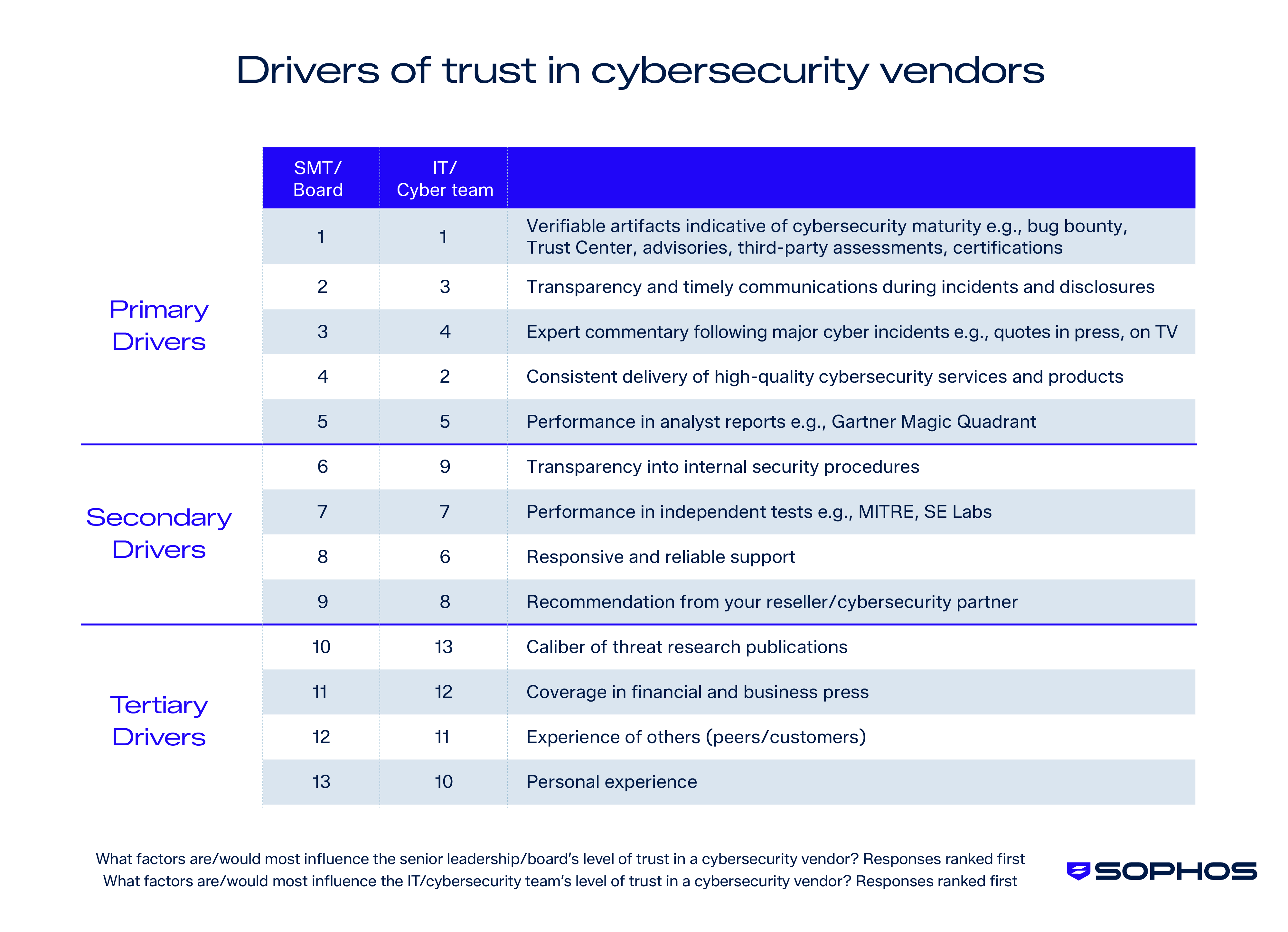
Respondents indicated that transparent, evidence-based security practices are central to building trust. Organizations want vendors who enable trust through openness, clarity, and evidence-backed security practices.
Across both senior leadership and IT teams, “verifiable artifacts indicative of cybersecurity maturity” ranked as the top driver of trust in cybersecurity vendors. These types of evidence include bug bounty programs, a public Trust Center, advisories detailing vulnerabilities in their products (along with how they were remediated), third-party assessments, and certifications.
“Transparency and timely communications during incidents and disclosures” also ranked as the second largest driver for SMT members and third among IT team members.
Sophos’ commitment to earning our customers’ and partners’ trust
At Sophos, we understand that trust is built — not claimed — and we work to earn it every day through transparency, integrity, and a steadfast commitment to protecting security and privacy.
At the heart of our efforts is the Sophos Trust Center where we publish security advisories, document product vulnerabilities and remediations, outline our compliance posture, and share how we protect customer data.
This transparency is also demonstrated in Sophos X‑Ops’ Pacific Rim investigation, which publicly documented a five‑year campaign by China‑based threat actors and shared detailed tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), and defensive guidance to help organizations strengthen resilience industry‑wide.
By exposing sophisticated nation‑state activity, working with governments and other vendors, and being candid about both strengths and weaknesses, Sophos reinforces that trust is something earned daily through honesty, accountability, and a commitment to safeguarding the broader digital ecosystem.
Learn more
For further information on our commitment to enabling trust and the resources we provide to help evaluate trust in Sophos, visit the Trust Center or speak to your Sophos partner or representative.
To explore these findings in PDF format, access the report here.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


