.avif?width=1024&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
Cloud workload protection
Protect every workload with unified security built for the speed and scale of modern cloud environments.

Secure cloud growth
Protect your infrastructure with runtime threat detection and prioritized investigations across your cloud environments, data centers, hosts, and containers.

Get performance and uptime
Flexible, lightweight host and container protection is optimized for performance. Available via agent or API to integrate with your security operations, IT, and DevOps processes.
Minimize time to detect and respond
Sophos XDR provides complete visibility into your host and container workloads, identifying malware, exploits, and anomalous behavior before they get a foothold.
- Extended detection and response (XDR) provides complete visibility across your hosts, containers, endpoints, networks, and cloud services.
- Cloud-native behavioral and exploit runtime detections identify threats, including container escapes, kernel exploits and privilege-escalation attempts.
- Streamlined threat investigation workflows prioritize high-risk incident detections and consolidate connected events to increase efficiency.
- Integrated Live Response establishes a secure command line terminal to hosts for remediation.
Integrate with security, IT, and devOps
Combat threats with actionable host and container runtme visibility and threat detections delivered through the deployment model that works best for your environment.
Lightweight Linux and Windows host agent
Secure your hosts and containers with a single agent managed through the Sophos Central management console. Easily investigate and respond to behavioral, exploit, and malware threats in one place and increase IT hygiene with automated detections, intuitive queries, and remote response.
Integrated Linux threat intelligence
Fine-tuned for maximum performance, seamlessly enrich your security operations workflows. Includes an ultra-lightweight Linux sensor that can be integrated into host and behavioral and exploit runtime detections via API and complements your existing automation, orchestration, log management, and incident response tools.
Get performance without friction
Uptime is your top priority. We provide lightweight security tools that can be integrated into your DevSecOps workflows to minimize risk and improve application performance.
Optimized for Linux
Identify sophisticated Linux security incidents as they happen without deploying a kernel module.
Eliminate Disruptions
Use a single agent optimized for resource limits (including CPU, memory, and data collection limits) to avoid costly downtime, overloaded hosts, and stability issues caused by traditional security tools.

Get flexible host and container protection
Protect your host and container workloads across Linux, Windows, hybrid, and multi-cloud environments.

Linux Security
Detection and resilience for Linux systems across container runtimes such as Docker, containerd, CRI-O, and other environments. Our detection is crafted with the threat models of cloud-native systems top of mind.

Windows Security
Secure your Windows hosts and remote workers against ransomware, exploits and never-before-seen threats, control applications, lockdown good configurations, and monitor changes to critical system files.

Hybrid and Multi-Cloud
Secure applications and data across your hybrid cloud footprint from a single console. The flexible agent runs on-premises, in data centers, hybrid and multi-cloud environments including AWS, Azure, GCP and Oracle Cloud.
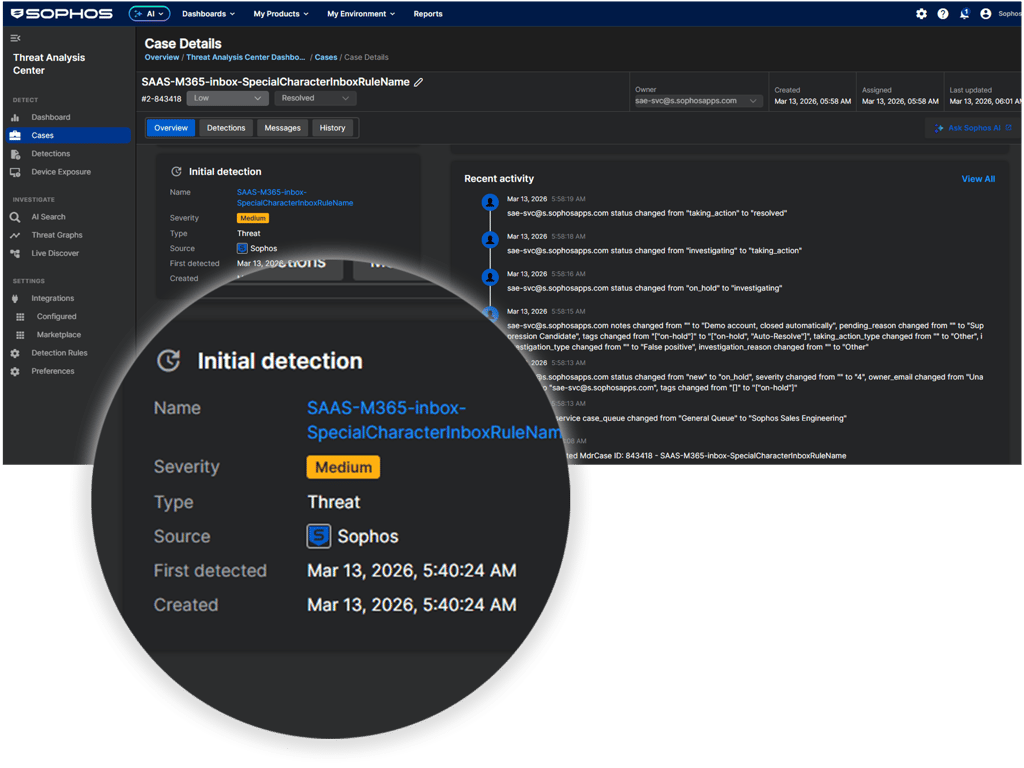
Resolve security incidents faster
Our intuitive detection dashboard increases incident response efficiency. Host and container threats are automatically identified and investigated, and an AI-prioritized risk score is provided for each detection. Scores are then color-coded and mapped against the MITRE ATT@CK framework, enabling security analysts to quickly prioritize, respond to, and remediate high-risk detections.
Detections include: Malware Targeting Linux, Memory Corruption, New File Behavior, Unusual Application Behavior, Suspicious Interactive Shell, Container Escapes, Kernel and Userland Backdoors, Privileged File Operations, Network Discovery, Lateral Movement, Process Injection, System Discovery, Scheduled Task Changes, Compiler Usage, Privileged Command Usage and Risky Developer Activity.
Hunt for threats and strengthen your IT operations
Get information that matters to you — right away. Choose from a library of pre-written templates for threat hunting and IT operations scenarios, customize them, or write your own. Access rich data from up to 90 days on disk and in the Sophos data lake to ensure you're covered for every scenario.
Popular customer use cases:
- Why is a workload running slowly? Is it pending a reboot?
- Which workloads have known vulnerabilities or unknown services?
- Are there programs running on the machine that should be removed?
- See unmanaged and unprotected devices such as laptops, mobiles, and IoT devices.
- Are processes trying to make a network connection on non-standard ports?
- Have any processes had files or registry keys modified recently?
- Which programs are causing office network issues?
- Analyze cloud security groups to identify resources exposed to the public internet.

Take the weight of cloud security off your shoulders
Our flexible approach to cybersecurity deployment and management means optimizing security, keeping data secure and private, while blocking active threats are goals you can easily achieve.
- Deploy and manage Sophos protection from a single unified console.
- The Sophos Managed Detection and Response (MDR) service can detect, investigate, and respond to threats targeting your cloud infrastructure, on your behalf.
- Sophos' Professional Services Team can help with initial deployment.

Respond to security incidents at 3 a.m.
The Sophos Managed Detection and Response (MDR) service delivers 24/7 threat monitoring, detection, investigation, and response for your cloud environment.- Threat Hunting: Proactive intelligence-led hunting to uncover hidden threats across your entire IT environment.
- Response: Remotely disrupts, contains, and neutralizes even the most sophisticated threats.
- Continuous Improvement: Get actionable advice for addressing the root cause of recurring incidents to stop them from occurring again.

.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
