Sophos Endpoint
AI-Era attacks stop here.
Sophos Endpoint is a unified Endpoint Protection and EDR solution built to defeat AI attacks. It blocks the techniques at the heart of attacks, stopping threats launched by either humans or Agentic AI tools. Powerful anti-ransomware, behavioral threat detection, exploit prevention, adaptive defenses, and threat surface reduction capabilities stop attacks before they occur.
of ransomware attacks start with an exploited vulnerability
of exploited vulnerabilities used in ransomware attacks are on a user's device
Source: Sophos research
Sophos has time and time again proven to be one of the most effective endpoint security platforms we have encountered, reliably performing and disrupting attackers at a level that simply outperforms the majority of the players in the next-generation antivirus and endpoint detection and response (EDR) space.
Jon Miller, CEO and co-founder of Halcyon



Sophos named a Leader in the 2025 Gartner® Magic Quadrant™ for Endpoint Protection Platforms
The endpoint is where AI-accelerated attacks land
AI now finds vulnerabilities and generates working exploits faster than most patch cycles can close them, and detection-first defenses are exposed when the payload is already running before the alert fires. The challenge is no longer whether attackers will reach your endpoints, but whether your defenses can stop techniques they have never seen, without per-application tuning, exclusion lists, or a security specialist on standby to keep protection enabled.

AI-accelerated threats
AI finds vulnerabilities and generates exploits faster than most patch cycles can resolve. Signature-based and detection-only defenses are exposed when new attacks emerge.

Detection without prevention
Detection-first products investigate too late in the attack chain. By then, the damage has occurred. You need to stop attacks before they execute, not after.

Operational drag
Multiple consoles, per-application configuration, and complex exclusion lists drain admin time. Strong protection should be enabled by default, not something to maintain.


A 2026 Gartner® Peer Insights ™ Customers’ Choice for Endpoint Protection Platforms
Sophos has been recognized as a Customers’ Choice vendor in the 2026 Voice of the Customer report for Endpoint Protection Platforms with a 4.9/5.0 overall rating based on 286 total reviews as of 30 November 2025

OVERVIEW
Prevention-first approach at the speed of AI
Agentic AI has collapsed attack timelines to seconds. Sophos Endpoint matches the attack velocity, automatically blocking exploits, ransomware, and attacker techniques by default with zero tuning, stopping threats launched by either humans or Agentic AI tools. Deep learning prevention, exploit mitigation, and CryptoGuard ransomware rollback combine in one lightweight agent that covers Windows, macOS, and Linux. Protection and visibility for endpoints, servers, and mobile devices.

Sophisticated protection built for the AI-era. Stop attackers in their tracks.

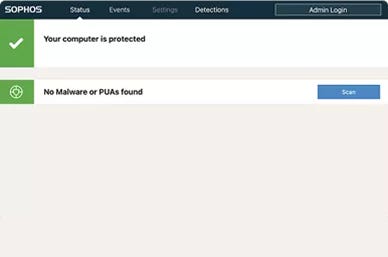
Default-on protection ensures the strongest defense. Easy to deploy and address drifts in security posture.
Shares real-time threat and health telemetry with the Sophos ecosystem, so a detection at any control triggers a coordinated response that contains attacks faster.
Engineered for what's next, proven against what's now
Anti-exploitation technology blocks the techniques attackers use, not the specific exploits they choose. 60+ proprietary mitigations are enabled by default on every running process, stopping threats launched by either humans or Agentic AI tools.
Govern your AI usage
Employees are adopting AI tools faster than security teams can govern them. Sophos Endpoint surfaces AI use and controls access to generative AI services. Security teams get the visibility and control they need to support AI adoption confidently, without slowing the business down.
Airtight ransomware protection
Adaptive Attack Protection
Critical Attack Warning
Synchronized Security
Sophos Endpoint shares real-time threat and health telemetry across the Sophos ecosystem, linking firewall, identity, and email, so a detection at any control triggers a coordinated response that contains attacks faster.
Extend your protection to the workspace
Sophos Workspace Protection extends protection to your apps, data, and remote and hybrid workers easily and affordably. Provide secure zero-trust connectivity, safe web browsing, data boundary controls, and insights into email threats.
Easy to set up and manage
Account health check
Poorly configured policy settings, exclusions, and other factors can compromise your security posture. The account health check feature identifies security posture drift and high-risk misconfigurations, enabling administrators to remediate issues with one click.
Protect all your endpoints
Get complete protection across all your desktops, laptops, servers, tablets, and mobile devices. Sophos Endpoint supports all major operating systems, including legacy platforms for critical systems.
Powerful protection built for the AI-era
Sophos Endpoint combines attack surface reduction, AI-powered prevention, exploit mitigation, and built-in detection and response in a single lightweight agent. Each capability is enabled by default, with no tuning required.
Reduce your attack surface
The fewer paths attackers have into the endpoint, the fewer threats your team must investigate later. Sophos Endpoint blocks malicious web traffic, controls which applications and peripherals can run, and surfaces shadow AI use, on and off the corporate network. Each control reduces your attack surface using the same lightweight agent.
Web Protection
Web Protection intercepts outbound browser connections and blocks traffic destined for malicious or suspicious websites. It stops threats at the delivery stage by preventing users from being diverted to malware delivery or phishing websites.
Web Control
Enforces acceptable-use policies on user web activity, including Generative AI usage. Restricts access to inappropriate content or unsanctioned AI tools, with allow, warn, or block actions per website category.
Application Control
Blocks vulnerable, unauthorized, or risky applications by category. Pre-defined categories, including Generative-AI tools, remove the burden of managing individual applications by hash. Restrict AI tool usage to reduce shadow AI risks.
Peripheral (Device) Control
Peripheral (Device) Control enables you to monitor and block access to removable media, Bluetooth, and mobile devices to prevent certain hardware from connecting to your network.
Data Loss Prevention (DLP)
Data Loss Prevention (DLP) monitors and restricts the transfer of files containing sensitive data. For example, prevent employees from sending confidential files home using web-based email.
Download Reputation
Download Reputation analyzes files as they’re downloaded and uses SophosLabs global threat intelligence to provide a verdict based on prevalence, age, and source, prompting users to block files with low or unknown reputation.
Prevention across the attack chain
AI gives attackers speed and scale, but exploitation still depends on a finite set of techniques. Sophos Endpoint blocks those techniques at every stage of the attack, before a payload runs, while it is running, and before it can complete its objective. Deep learning AI identifies known and never-seen malware before execution. 60+ exploit mitigations block the methods attackers use to turn a vulnerability into a compromise. Behavioral analysis catches threats that only reveal themselves at runtime.
Deep learning AI prevention
Sophos has a rich heritage in leveraging AI for protection. Multiple AI models identify known and never-seen malware before execution, including AI-generated and AI-mutated variants. Pre-execution scanning blocks payloads at the point of execution.
Anti-Exploitation (technique-based)
Over 60 Sophos proprietary exploit mitigations are enabled by default and applied to every running process. They block the techniques attackers must use to turn a vulnerability into a compromise, including AI-generated zero-days, with no per-application configuration.
Some vendors, including Carbon Black, SentinelOne, and Microsoft, lack extensive exploit mitigations or require significant manual tuning.
Behavior Analysis
Behavior Analysis monitors process, file, and registry events over time to detect and stop malicious behaviors and processes. It also performs memory scanning, inspects running processes to detect malicious code only revealed during process execution, and detects attackers implanting malicious code in the memory of a running process to evade detection.
Antimalware Scan Interface (AMSI)
Antimalware Scan Interface (AMSI) determines whether scripts (e.g., PowerShell or Office macros) are safe, including if they are obfuscated or generated at runtime, blocking fileless attacks where malware is loaded directly from memory. Sophos also has a proprietary mitigation against malware that attempts to evade AMSI detection.
Live Protection
Live Protection extends Sophos’ comprehensive on-device protection with real-time lookups to SophosLabs' latest global threat intelligence for additional file context, decision verification, false positive suppression, and file reputation. Our Tier 1 threat research provides additional live intelligence from Sophos’ expansive product portfolio and global customer base.
Some vendors including Carbon Black, CrowdStrike, and SentinelOne rely solely on pre-trained machine learning models.
Malicious Traffic Detection
Malicious Traffic Detection detects a device attempting to communicate with a command and control (C2) server by intercepting traffic from non-browser processes and analyzing whether it is destined for a malicious address.
Application Lockdown
Application Lockdown prevents browser and application misuse by blocking actions not commonly associated with those processes. For example, a web browser or Office application attempting to launch PowerShell.
Tamper Protection
EDR killers using bring-your-own-vulnerable-driver techniques are a common pre-ransomware step. Tamper Protection provides kernel-level self-defense that blocks interference with the Sophos agent. Defense evasions are caught before a malicious driver can act.
RELATED PRODUCTS AND SERVICES
Cybersecurity for all your needs
Sophos Endpoint Detection and Response (EDR)
Sophos Endpoint is included in Sophos EDR. Elevate your endpoint defenses with detection and response tools.
- Gain insights into evasive threats across your endpoints and servers.
- Includes powerful capabilities for IT operations and security analysts.
- Single agent for endpoint protection, detection, and response.
- Contain threats with accelerated and automated response tools.
- Multi-platform, multi-OS support.
Sophos Extended Detection and Response (XDR)
Sophos EDR is included in Sophos XDR: Empower your security team to defend against sophisticated multi-stage, multi-vector attacks with extended detection and response (XDR) tools.
- Accelerate investigation and response with AI-powered tools.
- Complete visibility across all key attack vectors.
- Integrate existing security and IT tools to detect and neutralize attacks.
- Leverage a fully integrated portfolio of Sophos products.
- Rapidly contain and remediate threats.
- Includes Sophos Endpoint and Sophos EDR.
Sophos Managed Detection and Response (MDR)
Free up IT and security staff to focus on business enablement and leverage superior security outcomes delivered as a service.
- Instant security operations center (SOC).
- 24/7 threat detection and response.
- Expert-led threat hunting.
- Full-scale incident response capabilities.
- Keep the cybersecurity software you already have.
- The most robust MDR service for Microsoft environments.
- Breach protection warranty.
.png?width=1024&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
Try Sophos Endpoint for free
We offer the world's best endpoint protection.
With Sophos Endpoint, you can:
- Access endpoint security that stops the broadest range of threats before they impact your systems and allows you to hunt, investigate, and respond to suspicious activity and indicators of attack.
- Automated responses to threats including automatic file rollback after encryption by ransomware and defenses that automatically adapt to the context of an attack.
- Use the Sophos Central cloud-based management platform to manage, view detections and alerts, investigate and remediate potential threats, and more across all Sophos products.
Get Started Today
Sign up for a free, no-obligation 30-day trial of Sophos Endpoint.
If you have an active Sophos Central account, you can sign up for a free trial of Sophos Endpoint and Sophos XDR from the Sophos Central Admin Console. To do so, log in to Sophos Central, then select "Free Trials," followed by "Sophos Endpoint Advanced with XDR."

See why customers choose Sophos

A Leader in the 2024 IDC MarketScape for Modern Endpoint Security for Small and Midsize Businesses

A Leader in the Gartner 2025 Magic Quadrant for Endpoint Protection Platforms for the 16th consecutive time

The #1-rated Endpoint Protection Platforms solution in the G2 Spring 2026 Reports

Industry-leading protection verified by independent third-party testing
Sophos State of Ransomware 2025 Report
How likely are you to be hit by ransomware? How many of your computers would be affected? Find these answers and much more in the Sophos State of Ransomware 2025 Report.
Customer Success
Already a customer? Find additional information to inspire, grow your knowledge, troubleshoot, and get help.
Frequently asked questions
Sophos Endpoint is a unified endpoint protection and EDR solution that blocks the techniques attackers use, rather than chasing the specific exploits or malware variants they choose. It combines AI-powered prevention, 60+ exploit mitigations enabled by default, CryptoGuard ransomware rollback, and built-in detection and response in a single lightweight agent for Windows, macOS, and Linux. It is managed from Sophos Central alongside the rest of the Sophos portfolio.
Yes. AI accelerates vulnerability discovery and exploit chaining, but the underlying techniques attackers must use to turn a vulnerability into a compromise are a finite, slow-moving set. Sophos Endpoint blocks those techniques with 60+ proprietary exploit mitigations, enabled by default on every running process, with no per-application configuration. The mitigations work whether the underlying vulnerability is known, unknown, or AI-generated.
CryptoGuard monitors file contents for malicious encryption and blocks the offending process, whether it runs on the protected machine or on a compromised network-connected device. The approach protects against new and novel encryption attacks, including remote ransomware against file shares, and automatically reverts encrypted files to their original state. Master Boot Record protection safeguards drives from ransomware designed to leave computers unbootable.
Sophos Endpoint enables 60+ exploit mitigations by default on every process, with no per-application configuration needed. Microsoft's strongest in-process mitigations are powerful but largely opt-in, requiring per-application audit-mode tuning and exclusion management that takes a trained Windows internals specialist to operate at enterprise scale. Sophos also extends beyond the endpoint with Synchronized Security across firewall, identity, and email, all managed from one console.
Most detection-first products are designed to detect and investigate after code is already running. Sophos Endpoint is prevention-first: exploit mitigation block at the moment of attack, so fewer threats reach your security analysts. Sophos also covers post-exploitation behaviors (credential theft, privilege escalation, persistence, ransomware payload) by default, not just initial exploitation. Independent recognition includes #1 in G2 Spring 2026 across Endpoint, EDR, and XDR.
Sophos Endpoint protects Windows, macOS, and Linux endpoints and servers, all from one lightweight agent. Coverage includes legacy Windows and Linux environments, which is operationally important for manufacturing, healthcare, government, and any estate with embedded or end-of-life systems where modern OS-level defenses are not available.
Yes. Strong protection is enabled by default, so SMBs without a dedicated security team get the strongest configuration without tuning, exclusion management, or per-application setup. The same agent and Sophos Central console scale up to mid-market and enterprise estates. SMBs can also add Sophos MDR for 24/7 expert oversight, delivered as a service.
No. The recommended protection technologies, including all 60+ exploit mitigations, are enabled by default on every protected process. There is no audit period to survive, no per-application policy to build, and no exclusion list to maintain to get the strongest configuration. Granular controls remain available for teams that want them, but they are optional, not required.
Sophos Endpoint provides prevention-first protection: exploit mitigation, deep learning malware prevention, CryptoGuard, Adaptive Attack Protection, web and application controls, and more. Sophos EDR adds AI-accelerated capabilities for threat hunting, investigation, and response, and includes Sophos Endpoint. Sophos XDR extends the capabilities of Sophos EDR with powerful tools and threat intelligence that enable you to detect, investigate, and respond to suspicious activities across your entire IT ecosystem, with an AI Assistant to help users of all skill levels to rapidly progress threat investigations and response.
Yes. Sophos MDR provides 24/7 threat detection, expert-led threat hunting, and full-scale incident response delivered as a service. It works with Sophos Endpoint and also ingests telemetry from third-party security tools you already have. MDR is appropriate for organizations without an internal SOC, and for security teams that want to extend coverage without adding headcount.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)