
The age of the corporate network and single security perimeter is coming to an end. Users are increasingly working remotely, conducting their work over the public internet. The rise of Software-as-a-Service (SaaS) apps, cloud platforms, and other cloud-based services has eroded the efficacy of using the network as the primary element to secure a resource. We can no longer rely on a single, sealed-off corporate network and afford trust to all the systems that reside within it.
Enter zero trust; a cybersecurity philosophy on how to think about security and how to do security. Zero trust is based upon the principle of “trust nothing, verify everything” and focusing on protecting resources regardless of where they are physically or digitally and to never trust anything by default.
No one vendor, product, or technology will get you to zero trust. Rather it requires a cultural shift and a lot of different solutions to shift the paradigms by which we secure our resources. This article looks at the concept of zero trust, the benefits of implementing a zero trust model, and provides guidance on the steps that organizations need to take to transition towards it.
What is zero trust?
Zero trust security is a model and a philosophy for how to think about and deploy cybersecurity solutions.
No one and nothing should be automatically trusted, be it inside or outside of the corporate network, even the network itself. Implicit trust based on network location, with static defenses like a traditional firewall, must be limited.
Eventually something needs to be trusted, but with zero trust, this trust is temporary and established dynamically from multiple sources of data, more than we’ve ever used in the past, and it is constantly re-evaluated.
We have plenty of experience with untrusted networks through our daily use of the internet. Computers that face the public internet are secured in a very different manner to those inside the traditional perimeter, requiring extra scrutiny and layers of defense to protect them from external threats.
The zero trust model guides you to treat all devices as if they were internet-facing and, instead of having one single perimeter, you must create micro perimeters, applying checks and controls around everything and between everything.
The core benefits of adopting zero trust
Adopting a zero trust model brings innumerable benefits, so, to make your life easier, we’ve picked out some of the core ones.
- Control of the entire IT estate
From inside the office all the way to the cloud platforms you use. No more lack of control outside the corporate perimeter or struggles with remote users. - Manage and secure all users in the same way
By no longer seeing things as inside or outside the corporate perimeter, you can treat all users in the same way. This both simplifies IT security while also ensuring all devices and users are treated equally. - Maintain security even when you don’t own/have full control over the infrastructure in use
By using identity, location, device health, MFA, and overlaying monitoring and analysis, you’re still able to have strong security across any kind of environment, platform, or service. - Drastically reduce the movement of malware or attackers
Rather than having free rein of the entire network once they’re inside, attackers only have access to the bare minimum of systems the compromised user had access to. By continuing to distrust the authenticated user, checks will be in place between those systems, further limiting the ability to spread.
A summary of Zero Trust
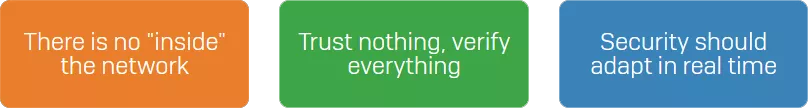
Zero trust is a big idea, and there is a lot of evolving discussion around it. At its essence, we can condense the major concepts for zero trust into several proverbs that you should keep in mind along your journey.
There is no “inside” the network
Pretend that you’re running your entire business from an untrusted location, like a coffee shop’s public Wi-Fi, and that all your devices are connected directly to the most dangerous of all networks: the public internet. By imagining this as your reality, you’re forced to apply security in ways where you can’t rely on being behind a traditional corporate perimeter.
Trust nothing, verify everything
Assume that there are attackers both on the inside of your networks and on the outside and they are there all the time, constantly attacking. No user or device should be automatically trusted and should authenticate itself before a connection can even be considered.
Security should adapt in real time
The security policies you put in place to achieve zero trust should be dynamic and automatically change based on insight from as many sources of data from as many different technologies as possible. A static policy won’t protect you if that device has been compromised while that user is on it. If your policy also took into account device health, such as the identification of malicious behaviors, your policy could use this to dynamically adapt to the situation.
Principles of zero trust
Trust nothing. Ever. For when you trust nothing, you are forced to seek relevant security measures wherever there is a risk.
Verify everything. Do not assume that passing a check naturally affords trust. Having credentials doesn’t mean you are trustable. It just means you have credentials. And credentials can be stolen.
We can break this into four simple principles to keep in mind.
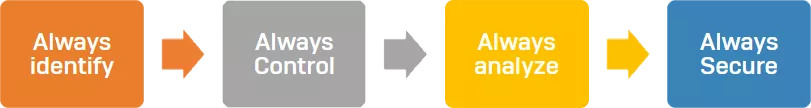
Always identify
You need a singular, authoritative source of identity and use it everywhere with Single Sign On (SSO). Everything should be authenticated, with multi-factor authentication (MFA). No matter where the user is, whatever they are trying to access, validate their credentials, validate they have their second (or third) factor, and regularly require re-authentication.
Always control
Apply controls and checks wherever they are needed and adopt and enforce the principle of least privilege – users should only have access to the bare minimum they need to perform their job. If there is a human resources system only used by German staff, then only the German staff should have access. No one else should have access, even if the risk of having access is deemed low.
Always analyze
Just because an authentication was successful, or access is granted to that user or device, doesn’t mean that it is trustable. Insider threats and malicious actors may gain access to valid credentials. Record all network and system activity and regularly analyze and inspect it to verify what occurs post authentication. SIEMs (security information and event management), EDR (endpoint detection and response) as well as MDR (managed detection and response) have emerged to serve exactly this need.
Always secure
Use an “inside out” approach to cybersecurity. You should focus on your important data and work your way out, identifying points of vulnerability along your data’s journey within your network from the moment it is created until the moment it is destroyed.
Once you’ve got a firm grasp of the principles of zero trust, you can begin to make the move towards it. You can read about this in the extended PDF version of the article.
The zero trust technology stack
It takes a lot of technologies to secure all the resources and assets you’ll have on a network. There is no one single vendor, product, or technology that will solve all your problems.
A zero trust technology stack needs to address two major areas – the management of zero trust, and the security and control of your various resources and assets.
Management is broken up into three sub-areas:
- Automation and orchestration – for defining dynamic policies, coordinating all the different technologies, and putting everything into place
- Visibility and analytics – for maintaining oversight of the network and ensuring everything is working as well as identify threats and breaches if or when they occur
- APIs – for integrating your various technologies together, getting data out of one system and into another
Resources and assets are broken down into five sub-areas:
- People – the users, admins, and others who work for or with your business
- Data – the lifeblood of all organizations, and perhaps the most important asset to secure
- Devices – the servers, laptops, virtual machines, etc. you use to conduct your business
- Workloads – the services and apps you use to process data, perform calculations, generate reports, etc.
- Networks – the communication channels over which data flows – web, email, Wi-Fi, the internet, and more
How Sophos can help
While a single vendor cannot move your organization to a zero trust model, Sophos has a huge range of technologies to help you get there.
The management of zero trust
Sophos Central, our cloud-native cybersecurity platform, enables you to manage a zero trust environment. It orchestrates all our technologies in a single console, providing you with oversight of all technologies in a single place and APIs to wire together any other third-party technologies you are using.
You also might consider a SIEM to aggregate logging from your non-Sophos and Sophos products to make it easier to have full oversight of what is going on. Our APIs make it easy to get information out of our Sophos Central platform and into whatever SIEM you’re using.
Controlled through Sophos Central, Sophos Synchronized Security also plays a big role here. With Synchronized Security enabled, Sophos solutions share information with one another and automatically respond to incidents. In the context of zero trust, solutions are able to adapt to scenarios through dynamic policy and automate complex tasks like isolating machines and more.
Security and the control of resources and assets
Many of our products help you secure multiple resources and assets at the same time, but by no means does that mean you can employ just one technology and move on. Securing people, for instance, requires a large number of different technologies as part of a resilient zero trust architected network.

Cloud Optix
can help secure within the public cloud, data, devices, workloads, and networks.

Intercept X
can help to secure all your resources and assets.






Sophos Firewall




Employing these technologies will put you in good stead when moving to a zero trust model. However, to empower your users to use cloud services wherever they are, you will additionally need a strong IAM solution with SSO in place to make use of your single authoritative source of identity across all systems and services. This is a key part of zero trust.
Conclusion
As it stands, zero trust is but a philosophy towards cybersecurity with very few able to readily embrace it. However, as security perimeters continually erode, the need for adoption will become increasingly prevalent. Cybercriminals are only growing more innovative and defenses are struggling to keep up with this. The zero trust model represents a way to truly minimize threats all the while setting new standards in cybersecurity protocol.
It’s time to think differently. It’s time to evolve.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
