Sophos (LSE: SOPH), a global leader in next-generation cybersecurity, today published the SophosLabs report MyKings: The Slow but Steady Growth of a Relentless Botnet, which details the morphing attack components of the globally-reaching MyKings cryptominer.
MyKings contains the perfect storm of attack methods highlighted in SophosLabs’ 2020 Threat Report – access through open remote services, botnets to orchestrate parts of the attack, and Living off the Land (LotL) to evade detection – that are used to drop cryptominers. The report covers the interaction between all of these components and their chain reaction to impact computers. The report also analyzes cybercriminal behaviors to further explain the characteristics of MyKings.
“High-end or nation-state sponsored cyberattackers have the resources to purchase or develop zero-day exploits themselves. On the flip side, low-end cybercriminals use cheap or free builder kits available in underground, dark web forums, but lack the skills to do anything except execute the builders,” said Gabor Szappanos, report author and threat research director, SophosLabs. “The MyKings group is in between these two categories; they are the ‘SMB of cybercrime.’ These criminals don’t invest money into expensive tools, but they have the skills and development power to modify and enhance open source components. Their modus operandi is to invest significant amounts of development time into customizing the public domain tools they are using. This is a reminder that cybercriminals are enhancing their capabilities all the time and defenders should adopt this mindset for best security practices.”
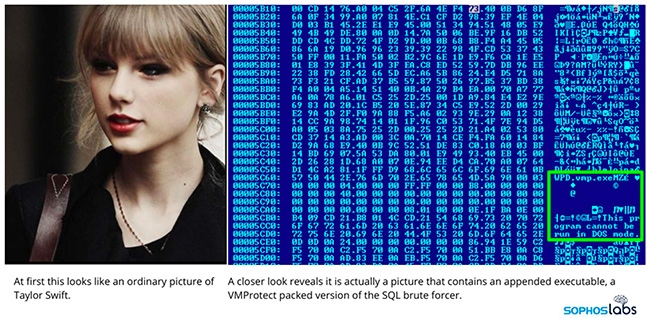
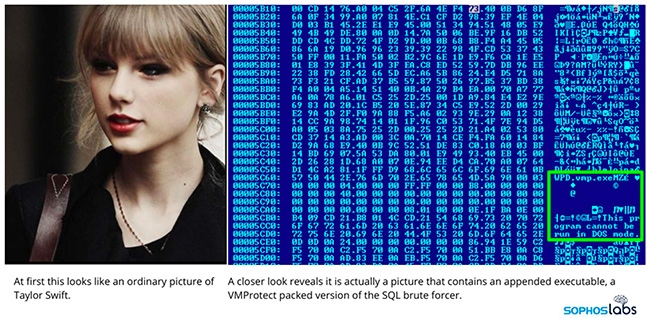
Below is an example of how the MyKings attackers enhanced the malware over time:
- Some older variants of MyKings download an update from
ww3.sin[…]g.cn/mw690/717a8b4dgw1f99ly7blarj20c40e4b2a.jpg
- Subsequently, cybercriminals added support for the EternalBlue exploit into newer versions of MyKings. This functionality is not integrated into the spreader program, but rather exists as a separate executable, converted from Python scripts, that is downloaded and executed by the main spreader program.
Global Distribution
As indicated in the MyKings report, the worldwide activity map includes approximately 45,000 impacted hosts. Top countries include: China, Taiwan, Russia, Brazil, United States, India, and Japan.
Other Key Findings
- The botnet can spread by attacking weak username/password combinations via MySQL, MSSQL, telnet, ssh, IPC, WMI, RDP, CCTV connections
- The main payloads are the Forshare trojan and various Monero cryptominers
- The botnet still mines about 5 XMR ($300), per day
Advice for Defenders
- Keep computers up-to-date with security patches. MyKings uses EternalBlue which was patched two years ago
- Change default passwords and apply strong, unique passwords. MyKings uses known weak passwords to attack web services
- Don’t expose Server Message Block (SMB), Remote Desktop Protocol (RDP) and similar remote access services to the Internet
- Use up-to-date security software. Sophos Intercept X provides protection at several points
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
