Secure Design
Security is at the heart of everything we do at Sophos. All development teams follow the Sophos Secure Development Lifecycle (SSDLC), a series of activities and roles that ensure all solutions are built securely and efficiently.
- We continually measure and improve all aspects of secure product development with the aid of the Open Software Assurance Maturity Model (OpenSAMM).
- We use state-of-the-art application security testing tools as part of the product development and release processes.
- Code scanning and fuzzing tools analyze code before deployment.
- We carefully track and manage the use of third-party components to ensure that any vulnerabilities can be addressed promptly.
- The Sophos security team works hand-in-hand with the development teams to ensure our solutions are defended from internal and external security threats.
All development takes place in a supportive, trusted environment. Build systems (including CI/CD pipelines) are treated like mature products and proper end-to-end key management ensures digital signatures are of high value and integrity. Our teams are empowered to respond to any kind of vulnerability or weakness in the environment, service, or product design, and in the product implementation.
SSDLC embedded in a trusted environment
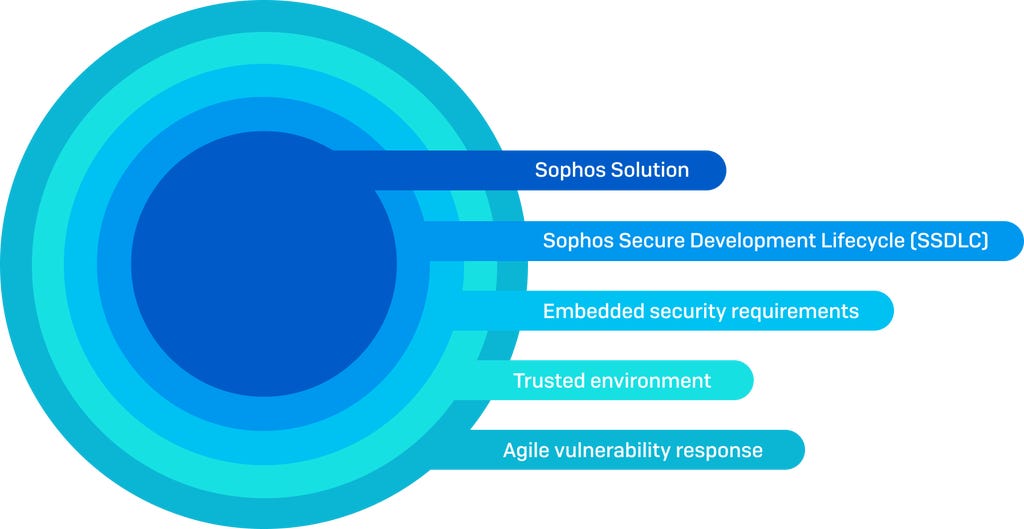
Our goal is always to provide customers with secure products and services. The Sophos Secure Development Lifecycle provides the framework for all product development activity. We embed security requirements in our product management processes and work hard to create a trusted and secure environment. This enables us to respond quickly and efficiently to any vulnerability.
Secure Chain of Custody

Software Bill of Materials (SBOM)
As part of our SSDLC process, we collect and maintain a Software Bill of Materials for all open-source and third-party components in many of our product codebases. This allows us to triage and identify any potential impact from emerging vulnerabilities in third-party complements included in our products. SBOMs also allow us to provide confidence to our customers that our products only contain components that are up-to-date and free from vulnerabilities.
For select products, Sophos can provide copies of our SBOMs upon request. For further details, please reach out to us via email at [email protected].
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
