Não seja a próxima vítima
Insights de ransomware e recomendações de defesa do líder em proteção global contra ransomware.
Ataques de ransomware são manchete há anos, criptografando e sequestrando dados até que um resgate seja pago. As vítimas desses sequestros variam de corporações multinacionais a hospitais e o público em geral.
Conheça o seu inimigo
66% das organizações foram vítimas de ransomware no ano passado. Não entre nessa.
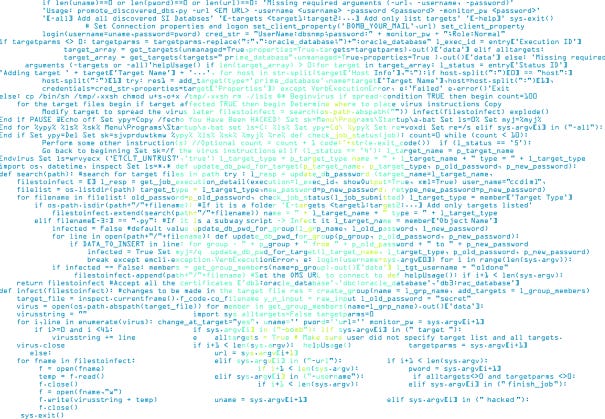
Ransomware remoto
Treine a sua organização
Os invasores sabem que basta apenas uma pessoa baixar a guarda para que a organização seja dominada.
Nosso kit de ferramentas para treinamento anti-ransomware para gerentes de TI oferece recursos gratuitos para treinar os usuários no combate a ransomware, incluindo uma lista de tópicos organizacionais, cartazes de conscientização em segurança e um vídeo educativo para funcionários.
Implante proteção de classe internacional
Os ataques de ransomware de hoje combinam várias técnicas avançadas com a invasão em tempo real. Para minimizar o risco de se tornar uma vítima, você precisa de proteção avançada que monitore e proteja toda a cadeia de ataque.
Sophos Endpoint
O Sophos Intercept X with XDR oferece as tecnologias avançadas de proteção que desmantela toda a cadeia de ataque. Enquanto o Deep Learning prevê e impede ataques, o CryptoGuard reverte a criptografia não autorizada dos arquivos em segundos.
Aplique as práticas recomendadas
Siga estas superdicas para minimizar um risco de ataque:
- Use autenticação multifator (MFA)
- Use senhas complexas
- Limite os direitos de acesso: dê a seus administradores e contas de usuários apenas os direitos de acesso necessários e nada mais
- Faça backups regularmente e mantenha-os fora de suas instalações e offline, onde os invasores não os encontrem
- Aplique os patches cedo, e sempre. Ransomwares como WannaCry e NotPetya aproveitam vulnerabilidades não corrigidas para se espalharem pelo mundo
- Bloqueie seu RDP. Desative o RDP se não precisa dele e, em vez disso, use limitação de taxa, 2FA ou uma VPN
- Assegure-se de que a proteção contra adulteração está ativada – Ryuk e outros ransomwares tentarão desabilitar a sua proteção de endpoint
Veja por que os clientes escolhem a Sophos para proteção contra ransomware




.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)




