What are data breaches?
Updated: December 11, 2025
Author: Sophos
Data breach prevention is a form of cybersecurity that is focused solely on stopping a data breach before it can take hold. A data breach is an incident resulting in the exposure of confidential, private, protected, or sensitive information. This includes corporate information, such as trade secrets or financial information, as well as personal data belonging to your partners, customers, and employees.
Why is Data Breach Prevention Important?
To be clear, any company can become the victim of a data breach. Data breaches happen to organizations of any size across every single industry. For organizations that experience a data breach, that cost can affect the financial health and longevity of the business. For the individuals whose data has been exposed, they must now live with the possibility that their personal identifiable information (PII), such as credit card account numbers, Social Security numbers, or personal health records, are now available on the internet for any variety of bad actors to exploit.
It’s up to you, as the organization that is handling, storing, and sharing all of this data, to prevent data breaches and PII from unauthorized access. For all of these reasons and more, data breach prevention must be a top priority for all security teams.
What Kinds of Data Breaches Should Raise the Most Concern?
The attack vectors behind data breaches are constantly evolving, but over the years, certain types of threats remain a constant that contribute to most data breaches. These attack vectors include:
Phishing attacks
The number-one goal of a phishing attack is to steal your users’ credentials, whether to a system, server, device, or application. If an unauthorized user gains access to your credentials, they have the keys to simply walk in the front door of your systems without being detected. A phishing attack starts by sending a reasonably convincing email message to a target. The email includes some kind of call to action that tricks the target into clicking on a malicious link. For example, your user receives an email that appears to be instructing them to change a password. That URL leads to a phony website where they’re asked to enter their credentials. The victim never suspects that they’ve just handed this information over to a bad actor.
Ransomware attacks
Another form of email-based attack, ransomware also uses phishing as a mechanism to inject a harmful malware into a system. Ransomware involves luring the victim to click a link or download an email attachment. What the target doesn’t realize is that ransomware code is embedded into that link or attachment. Once the victim clicks the harmful link or opens the attachment, the ransomware is downloaded automatically. The malicious software then restricts users from accessing their IT systems, such as servers, workstations, mobile devices, or databases, unless they pay the attacker a ransom.
Social engineering attacks
This data breach attack vector uses manipulation and deceit to trick users into making security mistakes. They often involve the impersonation of another person or a company. Typically, social engineering attacks occur in multiple steps. First, the attacker scopes out the intended victim in order to gather necessary background information, such as potential endpoint security weaknesses. Next, the attacker uses false pretenses to gain the victim’s trust. Any company can be at risk of social engineering attacks; in fact, one of the biggest involved a nation-state actor who targeted Google and Facebook employees and resulted in the loss of $100 Million between the two companies.
Software misconfigurations and exploited vulnerabilities
Security misconfigurations happen when essential security settings in enterprise software are not implemented properly or updated regularly. Research shows that 47% of active attacks began with an exploited vulnerability. Misconfigurations can create dangerous security gaps that leave applications, systems and data open to a breach. Software misconfigurations are a common point of entry. They can happen anywhere in the application stack, including web or application servers, databases, network services, storage, and virtual machines.
Human error
Human error is a common factor in data breaches. Examples include accidental actions such as losing a corporate laptop, downloading a malware-infected attachment, failing to use a strong password, or neglecting to update software.
How is Data Breach Prevention Different from Data Loss Prevention?
The difference between these two cybersecurity terms is subtle, but important. Both strive to stop the exposure of sensitive information. However, data loss prevention is focused on stopping data from leaving the organization entirely. It’s intended to prevent sensitive data from leaving the security perimeter of a company and flowing outside of it. Historically, data loss prevention is built around a more static, defined enterprise network. Its focus is protecting data in motion and providing a layer of protection at the network edge.
In contrast, data breach prevention is a more holistic approach that provides a layer of data security both internally and externally, both in motion and at rest. Data breach prevention strategies are built on the reality that traditional network perimeter protection is no longer enough, especially with the rise of remote work, cloud computing, and the proliferation of connected devices. Websites and business applications must maintain a certain level of resilience and good cyber hygiene to combat the sophisticated attacks they face today.
How Does Data Breach Prevention Work?
It’s wise to take a holistic, layered approach to data breach prevention that addresses all common points of security weakness. And that must include data that is stored and shared via the cloud, on remote devices, and various other endpoints. In today’s complex environment, a potential breach could happen at any time, at any point in your organization’s infrastructure.
A successful data breach prevention strategy provides protection at each layer of the IT infrastructure:
- Endpoint - This applies to all connected devices, both inside and outside the corporate firewall. Endpoint security is the “front line” of the data breach attack surface.
- Network - It’s important to protect the enterprise network from known and unknown threats that are brought into the perimeter though the internet. At the same time, you still need to accelerate and prioritize SaaS, SD-WAN, and cloud application traffic.
- Email - Like it or not, email is the way work gets done. That’s what makes phishing attacks resulting in business email compromise (BEC) so devastating for companies. Data breach prevention for email means your employees can trust their inbox. Email security should protect your people and critical information from malware, phishing, and social engineering attempts.
- Cloud - Today’s organization operates in a multi cloud environment. That includes AWS, Google, Azure, Kubernetes, and more. This offers greater flexibility but creates a significantly larger attack surface. Data breach prevention must support multi-cloud security coverage across environments, workloads, and identities.
The focus of data breach prevention should be on securing these four layers without hindering productivity.
How Important is Data Breach Response?
The ability to detect a breach before attackers can cause damage is extremely important. Awareness is the first step, but you also need an established plan of action to respond. Having an incident response game plan for responding to threats helps organizations learn from their mistakes and prevent future incidents. Once a threat to your data has been introduced, your incident response must be timely and achieve the crucial goal of stopping the attack before it can cause significant damage.
Time-to-detection is essential in a security incident scenario. Detecting and responding quickly to a potential data breach is crucial because slow responses can result in fines from regulatory bodies, along with the deterioration of customer trust.
What Are Some Data Breach Prevention Best Practices?
The best data breach prevention solution must have the power to provide:
- Accurate, real-time visibility of all assets across the organization: Identify all areas inside and outside of the network perimeter that store, transmit, collect, or process sensitive data. Endpoint security is a significant element of any data breach prevention solution.
- Strict access control to networks, systems, and applications: Protect user credentials from falling into the wrong hands.
- Regular maintenance of software integrity (i.e. patch management, software updates): Prevent misconfiguration vulnerabilities and shrink your organization’s attack surface.
- Strong security hygiene of all connected devices, including remote and mobile devices. Work-from-home is here to stay. The new data breach prevention strategy must protect devices everywhere.
- Enforcement of multi-factor authentication for all of your security administrators.
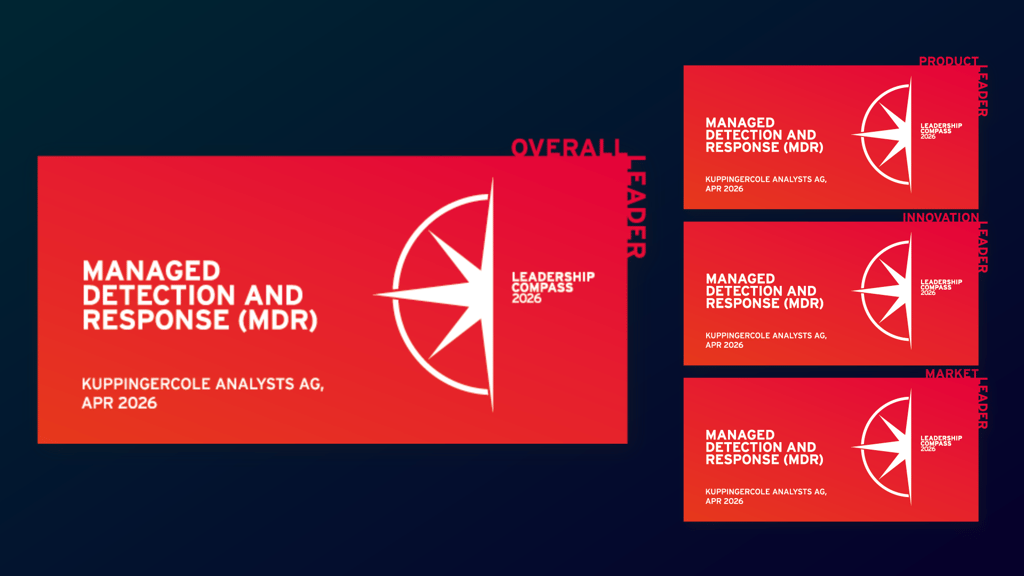
- Detection and response to act swiftly in the event of security incidents before they can take hold. This can include managed detection and response (MDR).
- Proper encryption of data in motion and at rest.
- Regular employee training to arm your users with knowledge. Detection of a data breach is often a key indicator that your users are in need of more training, especially when it comes to phishing and social engineering attacks.
Data breach prevention requires constant vigilance. As threats continue to advance, organizations need to be flexible enough to add more protection. Security pros must continuously audit and reevaluate the team’s efforts. For example, has your CISO handed down new security practices or regulations to follow? Do you have a greater number of new users joining the network? Are you supporting more remote workers?
How to Improve Your Data Breach Protection Strategy
While you may not be able to prevent every attack, you must make every effort to do so. That requires a strong data breach prevention strategy that is continuously evolving.
One way to build and maintain a strong data breach prevention strategy is to outsource some or all of your security to a managed security service provider (MSSP). By partnering with a trusted data breach protection partner who is monitoring your systems continuously, your organization can detect bad behavior faster and gain an advantage over attackers before they have a chance to do any damage.
No two businesses, IT security teams, or environments are alike. Your best course of action is to perform a thorough security audit. As you consider security solutions for any weak points in your current systems, think about the way the people in your organization are working today, how they will work in the future, how they share information, and how data flows in and out of your enterprise infrastructure.
A cybersecurity audit will help you ensure that your solution addresses the most critical aspects of data breach protection at every layer of your infrastructure.
The expert team at Sophos can help you understand which data breach prevention solutions work best for you. To learn more about our approach to data breach prevention, get in touch today.
Related security topic: What is cyber risk management?
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)